This article is more than 1 year old
The application platform’s in play. But where’s it going?
Strategy or tragedy, according to Reg readers
Reg Tech Panel This application platform thing looks like it has legs. A few weeks ago we asked the Reg audience at large if they ‘got’ the idea of the application platform, and, practicalities aside, most said ‘we do’.
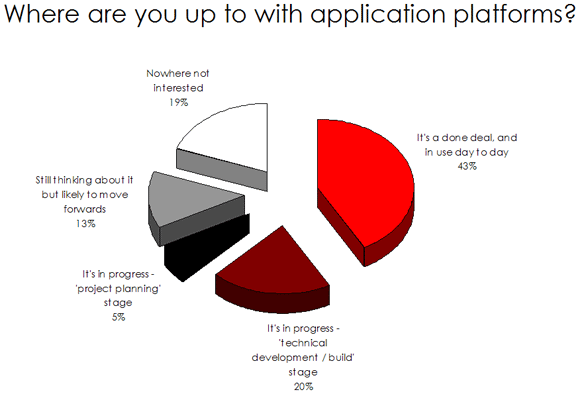
Around a quarter said they had already adopted one. Digging a bit further, we see that of those that are ‘somewhere’ with their application platforms - nearly half see it as a done deal and in play. Now, given the self-selecting nature of online polls, we’ve not kidding ourselves that 43 per cent of the Reg audience has this area all sewn up - but even if we consider them to be a subset of those that get the idea, that’s still quite a lot of application platform action going on.
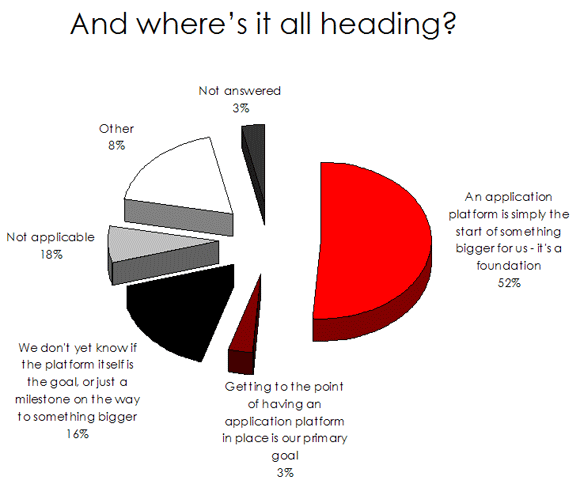
So where is all this heading? Just over half of you who took part in our last mini poll said the application platform is simply a means to an end. Another 16 per cent are still deciding if it’s the goal in itself, or just a milestone on the way to something bigger. Does it surprise anyone that the application platform is not a goal in itself, as just three per cent told us?
Standardising across this relatively broad area is surely an achievement in its own right. Then again, given that people are subscribing to the idea, it’s clear that they are thinking beyond ‘just’ a standardised platform, and how it could be leveraged to allow more focus on developing truly differentiating business logic for application front ends.
But it’s not all plain sailing. The concept of the application platform has its critics: and the primary objections are that it is an unnecessary complication, and worse, just the latest fashionable buzzword designed to extract hard-earned cash.
Others see it as a place where ‘some’ applications will live, but perhaps not all of them. This is a fair point, perhaps, especially as we already considered if the degree of support available for these things could limit their scope. It remains to be seen as to whom is proven right.
The opportunity to point and laugh, or be impressed by the gains made by the early adopters will come soon enough. As we’ve acknowledged, there are quite a few organisations up and running already. In terms of experiences so far, as usual, we’d love to hear about any amazing benefits or shocking surprises you’ve encountered… ®
