This article is more than 1 year old
Schoolboy bags $10,000 reward from Google with easy HTTP Host bypass
Nice birthday gift for clever kid who found a way to access web giant's confidential info
A teenager in Uruguay has scored big after finding and reporting a bug in Google's App Engine to view confidential internal Google documents.
While bored in July, high schooler Ezequiel Pereira, who has all the makings of a competent security researcher, used Burp to manipulate the Host header in web connections to Google's App Engine. The 17-year-old's target: webpages protected by MOMA, Google's employees-only portal apparently named after a museum of modern art.
Normally, connecting to a private staff-only Google service requires signing in via MOMA. However, it appears not all of these services fully checked a visitor was authorized to view the content.
By connecting to a public Google service, such as www.appspot.com, and changing the Host header in the HTTP request to, say, yaqs.googleplex.com, Pereira was redirected to Google's internal project management system YAQS. Viewing that system should have required a MOMA sign-in, but instead, he was able to view YAQS pages marked "Google confidential."
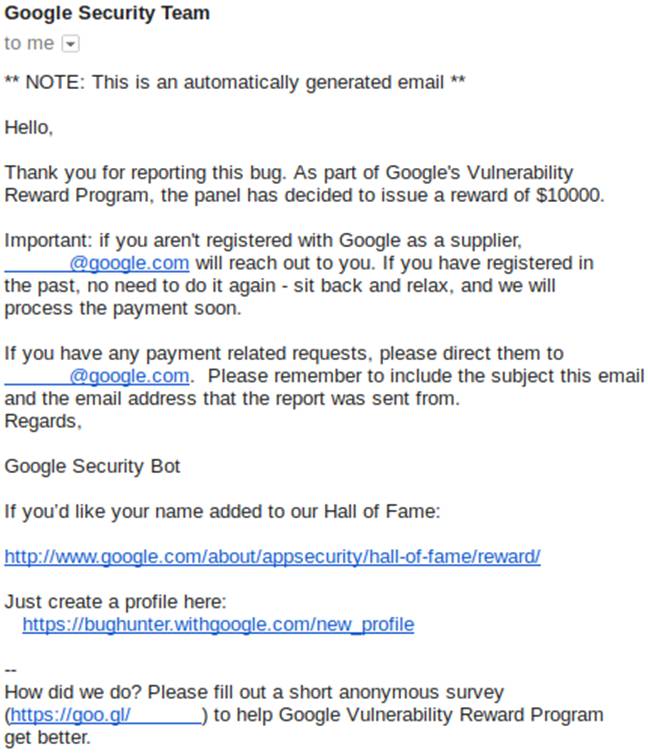
The student reported the loophole to Google on July 11, and on August 4, about a month before his 18th birthday, he was told the issue had been fixed and that he had earned a $10,000 reward from the ad giant's bug bounty program. Pereira, who has previously earned a few thousand of dollars for reporting vulnerabilities to Google, was stunned by this single payout.
"I just think it was a very simple bug and I didn't expect the large bounty at all," he told The Register on Thursday. "Maybe I'll learn how to invest it, maybe I'll travel somewhere nice and do some tourism."
A couple of years ago, Pereira won Google's annual Code-in programming competition for pre-uni students, earning him a trip to San Francisco and the Googleplex in California. Clearly, he couldn't tear himself away from the place, poking at internal services via the App Engine earlier this year.
"Most of my attempts failed, either because the server returned a 404 Not Found, or because it had some security measure such as checking that I used a Googler account (username@google.com) instead of a normal Google account," he explained this week.
"But one of the websites I tried, 'yaqs.googleplex.com', didn't check my username, nor had any other security measure. The website's homepage redirected me to "/eng", and that page was pretty interesting, it had many links to different sections about Google services and infrastructure, but before I visited any section, I read something in the footer: 'Google Confidential.'"
Once he saw that, Pereira said he backed out immediately. While he didn't think it was a serious issue, he pinged a bug report about it to the Chocolate Factory just to let them know. The teen got a response that day from Google thanking him. He thought no more of it but then got the following message just under a month later:
It seems Google researchers found out that the vulnerability could be used to access some very confidential data indeed. It was presumably so serious that Google felt ten large was a suitable reward.
For a schoolboy in Uruguay that's a serious amount of cash – it's five times the average monthly salary. We think we'll probably be hearing from Pereira again in the near future. ®
