This article is more than 1 year old
Have a go with this WW2 German Lorenz cipher machine – in your browser
Fancy a crack at being Germany's secret signalman?
The National Museum of Computing has put an emulation of an "unbreakable" Second World War German cipher machine online for world+dog to admire.
The Virtual Lorenz machine has been launched in honour of WW2 codebreaker Bill Tutte, the man who broke the crypto used in the twelve-rotor cipher machine.
As The National Museum of Computing (TNMOC) puts it, Tutte's work "shortened the conflict" – even though he had never even seen the cipher machine or its crypto scheme, the breaking of which the museum added was "the greatest intellectual feat of the war".
TNMOC unveiled the Virtual Lorenz today to celebrate Tutte's 100th birthday. Built by computing chap Martin Gillow, the simulation accurately reproduces the whirring of the cipher wheels (you might want to turn it down as the "background whirr" is a little too realistic).
The BBC profiled the "gifted mathematician" a few years ago, highlighting how the Lorenz machine whose secrets Tutte cracked was "several degrees more advanced than Enigma", the cipher famously cracked by Tutte's colleague Alan Turing. Tutte cracked the Lorenz in about six months, reverse-engineering its workings by reading intercepted Lorenz messages. When the Allies wanted to fool Hitler into believing the D-Day landings would take place in a false location, our ability to read Lorenz was critical for confirming that the ruse had worked – saving thousands of soldiers, sailors and airmen's lives.
You can set the Virtual Lorenz off with pre-filled text and watch it encrypt the message in real time (warning, we did this and couldn't find a way to stop it) or even write your own message and ping it to your mates. You can even import and export yours and your mates' key settings and connect directly to their machines, for that added thrill of cipher-text authenticity.
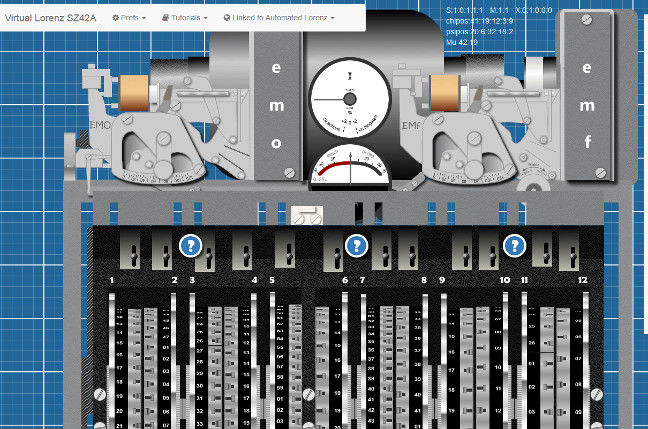
You'll need a lot of screen real estate to see the whole thing in its glory – this is only about a quarter of it
Full tutorials are available for those who want to learn to use the cipher machine properly, in the same way that German High Command signal operators used the original SZ42 during the latter part of the Second World War.
The Virtual Lorenz was born out of a project to update TNMOC's existing Virtual Colossus simulation.
Gillow explained: "As a programmer, I was fascinated by the rebuild of Colossus computer when I first saw it at The National Museum of Computing. Tony Sale, who led the rebuild team, had also created a Virtual Colossus for the web, but I discovered that it would only run on old browsers. Since Tony Sale had passed on, it was likely to become inaccessible and lost forever as web technologies progress.
"So, I decided to recreate the Virtual Colossus – and then a Virtual Lorenz to accompany it. It took months of work in my spare time, and revealing it to the audience at the Museum was a real thrill."
The Virtual Lorenz can be found here. Word to the wise – it's not on an HTTPS site, so if you're hoping to use it to thwart GCHQ, you might want to think again. ®
