This article is more than 1 year old
Microsoft's DRM can expose Windows-on-Tor users' IP address
Anonymity-lovers best not watch movies as .WMV files
Windows users running the Tor browser can be tricked into uncloaking themselves, with a pretty straightforward trick based on Microsoft's DRM system.
The discovery was made by Hacker House, which says it's been researching social engineering attacks made using DRM-protected content.
What the UK-based security outfit found is that a pretty straightforward bit of social engineering – “click on this media file” – can, at the very least, reveal the user's real IP address.
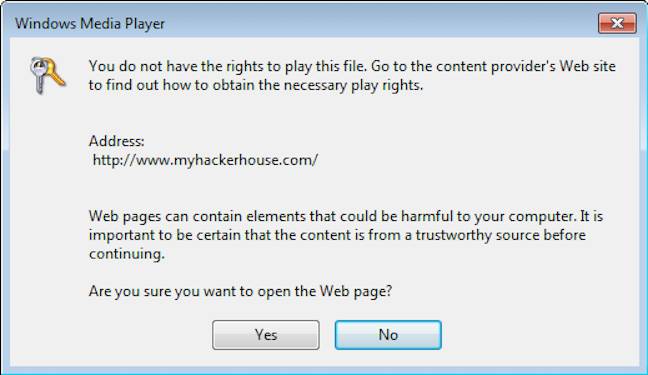
Here's what's going on: DRM-protected media has to fetch its licence key from a server. If it's not signed properly, Windows raises a dialogue to warn you.
“However, this warning DOES NOT appear if the DRM license has been signed correctly and the Digital Signature Object, Content Encryption Object and Extended Content Encryption Object contain the appropriate cryptographic signing performed by an authorised Microsoft License Server profile”, the author writes.
Hide this dialogue, capture a Tor user's IP address
Microsoft sets high barriers to entry for those who want to start signing media: “If you want to build your own Microsoft DRM signing solution the price-tag is around US$10,000,” Hacker House notes.
What they've seen in the wild is someone managing to generate signed content, apparently without paying that toll.
“As these “signed WMV” files do not present any alert to a user before opening them they can be used quite effectively to decloak users of the popular privacy tool TorBrowser with very little warning”, they write.
The risk that media files could expose users is known to Tor, which warns users to run Tails if they want to run media files.
It's not the first time people have seen social engineering attacks based on media files: the old “you need a plug-in to play this file” strategy had a Windows DRM variant back in 2013, according to Virus Total. ®
