This article is more than 1 year old
Fused box: Look who's containerizing storage, security and apps
We take a look at a couple of startups and their hype
Comment Containerized apps will gravitate to using containerized system services such as storage and security.
In the DevOps world, containerized apps run inside hosts, and system services such as security and storage are containerized as well. Outside that ideal world, these services are often linked to containers by some interface code, and new-world containerized apps are thus enabled to use old world storage and security.
Startups such as Minio and NeuVector say they are reinventing storage and security as containerized entities and, they claim, their tech will make it easier for developers to hook storage capacity and security mechanism into their containerized apps.
In the storage world, several suppliers have ways to add persistent storage to stateless containers; Atlantis,* CloudByte, Nexenta and Red Hat, for example.
What’s Minio got that’s special?
The company offers what it calls the open source “MySQL of object storage” and its now generally available µServer product is lightweight code that runs as VM or in a container on on-premises COTS servers and storage. Cofounder Anand Babu (AB) Periasamy says: “More than 90 per cent of our downloads are happening on Docker. We provision object storage as containers. Minio is involved as a service.”
One thing Minio has going for it is popularity, with more than 455,000 Docker pulls. Its feature set includes:
- Amazon S3 compatibility with support for both S3 v2 and v4 APIs.
- Data protection – Minio withstands failure up to half the number of servers and drives using erasure-code and bitrot protection capabilities.
- AWS-compatible lambda functions are supported for actions like thumbnail generation, metadata extraction and virus scanning. Notifications are supported through various popular frameworks (AMQP, Elasticsearch, Redis, NATS, WebHooks, Kafka and Postgres) and natively over HTTP long-polling.
- Replication.
- Auto-expiry.
It can be downloaded here.
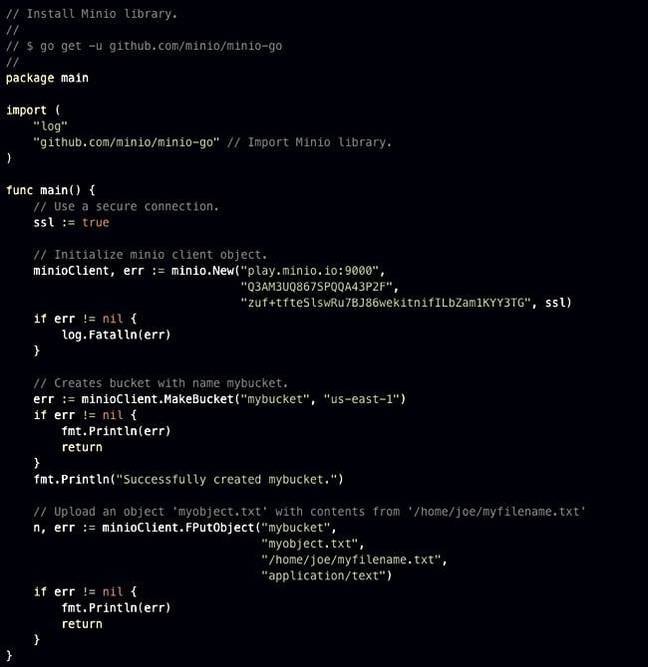
Code examples showing Minio use
Security
NeuVector says containers offer a new attack surface for malware people. For example, its Container Security Guide suggests there could be a “SQL injection attack to gain ownership of a database container to start stealing data,” or a “shell-shock bash bug allowing remote attackers to execute arbitrary code inside a container.”
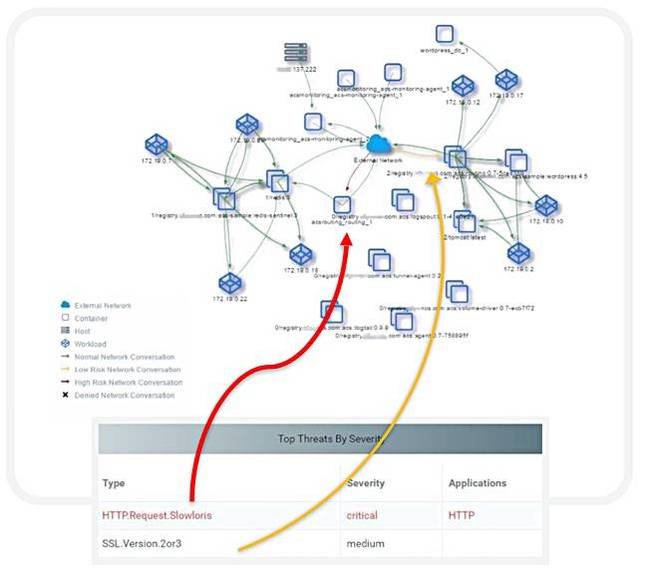
Its product response for container security is itself a container. It needs zero configuration and provides application layer segmentation that completely isolates container traffic, and offers a run-time learning approach to keep itself updated with security threats. NeuVector says it provides a distributed firewall for containers, with application layer intelligence providing true L3-L7 network inspection.
We’re told NeuVector’s security container app “automatically learns and whitelists normal behavior to protect environments even as containers scale up and down.” It claims: “Any abnormal connections can ... be proactively and automatically detected and blocked before causing harm. [There is] runtime vulnerability scanning across all running containers and hosts, and ... includes threat detection for attacks such as DDoS, DNS, and others.”
Fei Huang, CEO of NeuVector, sells his approach this way: “In order for security teams to keep up with DevOps, they can’t be running around inspecting iptables and updating rules. What we’ve designed is a security container that is intelligent enough to understand – in real-time – what applications are doing. There’s not a faster, easier, and more secure way to ensure Docker container environments are protected from unwanted or malicious traffic.”
The company claims “NeuVector can block only suspicious container traffic without affecting good traffic to the container” which is “unlike other false-positive-prone container security offerings.”
Michael Mueller, director of technology at Container Solutions, says the NeuVector product is “simple to deploy onto new or existing applications without requiring coding or agents.”
Steve O’Donnell, CIO of integrated security company G4S, says: “I need security compliance without compromising the proven agility and speed to market of our container-centric DevOps processes. So we’re looking at a DevOps approach to providing security for containers, a containerized security service for use by containers as just another container service.”
The image above shows a container security audit. It has run for 48 hours and found two threats, multiple sources and targets, and 138 high-priority vulnerabilities.
For new-world containerization devotees, the more they can access native containerized services for system-level functions like security and storage the better. Minio and NeuVector say they, literally, speak the DevOps language, inhabit the DevOps culture and believe its philosophy. In their world view the way to grow is through the hearts and minds of developers, and not by winning business from old-school enterprise IT departments.
Atlantis and Nexenta understand this view and have created DevOps-style versions of their storage products. We expect other security product suppliers to follow in NeuVector’s footsteps. ®
* Atlantis has partnered with Rancher Labs to build a software product to manage and provision compute, networking, storage and data services for containers.