This article is more than 1 year old
VMware's secret security plan revealed
Imagine a whitelist-checker running in the safety of the hypervisor kernel and monitoring VMs in real time
VMware has shown off a working prototype of “Project Goldilocks”, its long-hinted-at plan to develop a new approach to security.
The new idea is inspired by the NSX network virtualisation product's ability to create network “microsegments”, isolated virtual networks walled off from the rest of the network in a “least privilege environment” that only permits communications set in policies. Microsegmentation's popularity has taken VMware by surprise, but users like the way it lets them create virtual networks that just can't get to the outside world as restricted comms means that even if malfeasants get in, they struggle to get out. And because microsegments are virtual, they can be snuffed out while attackers are inside.
VMware's security plan riffs on microsegmentation and brings its concepts to securing compute and data.
The idea is explained in this video of a VMworld session* delivered by Tom Corn, VMWare's senior veep for security products. In the hour-long talk, Corn offered the opinion that endpoint security has scarcely advanced in recent years, or even decades. While endpoint security stood still, Corn says, everything else has become vastly more complex which means current approaches to security struggle to cope. Some policies are simple – web servers don't need to talk to storage – but implementing that policy when apps cross the data centre perimeter to reach other resources creates immense complexity. Cord said this complexity means firewalls can sometimes be asked to run 23,000 rules.
Project Goldilocks calls for applications to instead be given a “birth certificate” when they are in their gold state. That certificate should include all permissible behaviour for that application, detailing the expected executables, network infrastructure the app will touch, the ports it will use to reach that network and anything else that describes the application's state.
VMware then proposes to monitor all of those expected behaviours from within the hypervisor kernel, a location chosen because it is a different trust domain to the host or guest VMs. Corn said it's hard to detect wrongdoers, and harder to stop them, from the same trust domain as an attacker.
From its just right vantage point in the hypervisor kernel Goldilocks will monitor what Corn called a “manifest” of all expected VMs' “birth certificates” and provide “attestation services” that monitor the guest OS kernel, processes and communications. If the VM displays behaviour not explained in the manifest, up goes a red flag!
Here's how the console reporting on VMs looks in the Goldilocks demo.
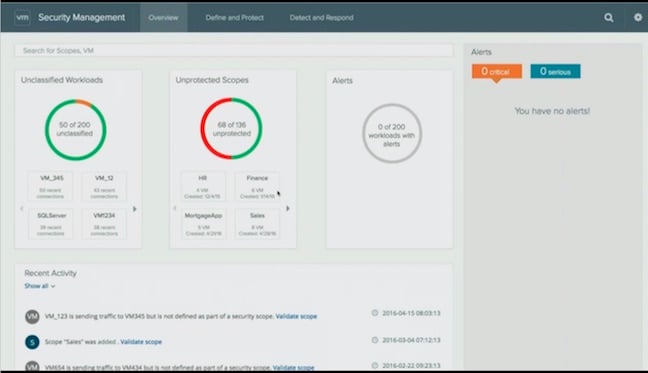
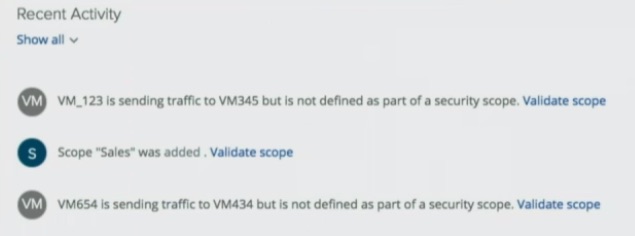
And here's a close-up of the reporting it produces.
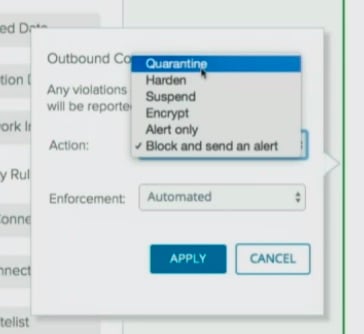
And here's what happens next: once sysadmins or folks in the security operations centre receive alerts about unexpected behaviour, they'll get options to quarantine, harden, or otherwise intervene in a VM's operations.
Corn also said VMware hopes to apply a similar approach to data, again planning to describe data and its expected uses and destinations before enforcing policy about how to encrypt or otherwise protect it when passing over networks that have the potential to be compromised.
When you've got a hammer ...
When you have a hammer, the old saying goes, everything looks like a nail. And it's often been observed that to VMware any problem looks like it can be knocked into shape with virtualisation.
Yet Corn's ideas are interesting because most of todays computing infrastructure was built to be open and then secured afterwards. Hypervisors were designed to offer a more constrained environment. So maybe VMware is on to something here.
One thing Corn did not mention is when Goldilocks might become a product. But the video depicts real code running live, so clearly VMware is a fair way down the road towards having something to sell. We'll try to figure out what's on the way and when. ®
* A session that co-incided with a Michael Dell press conference, wasn't repeated at VMworld and has only just appeared online in the last few days. Apologies also for fuzzy screen grabs, which are an artefact of the video quality on offer.
