This article is more than 1 year old
Hackers unleash smart Twitter phishing tool that snags two in three users
Just. Don't. Click. On. Dodgy. ShortURLs. People.
Black Hat Twitter scammers have a new weapon with the release of an effective spear phishing tool that lands a victim almost two thirds of the time, dwarfing the usual five-to-fifteen-per-cent-open-rate for spam tweets.
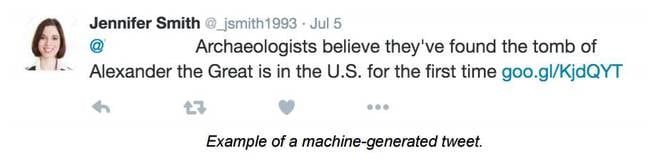
The SNAP_R machine learning spear phishing Twitter bot is a data-driven menace unleashed at the Black Hat security conference that is capable of consuming information from victim tweets to target users.
Creators John Seymour and Philip Tully of Baltimore security firm ZeroFox say the neural network is the world's first end-to-end Twitter pwn cannon useful to scammers, penetration testers, and staff recruiters.
"The model is trained using spear phishing pentesting data, and in order to make a clickthrough more likely, it is dynamically seeded with topics extracted from timeline posts of both the target and the users they retweet or follow," the researchers write in a paper titled Weaponising data science for social engineering: Automated end-to-end spear phishing on Twitter [PDF].
"We augment the model with clustering to identify high value targets based on their level of social engagement such as their number of followers and retweets, and measure success using click rates of IP- tracked links.
"Taken together, these techniques enable the world's first automated endto-end spear phishing campaign generator for Twitter."
Twitter is an incubator of phishing thanks largely to the prevalence of typos and shortened URLs that make it hard for users to know exactly where links are taking them. Plenty of phools phall for incoming spam links that send them nowhere good.
The tool, available as a downloadable zip archive, can be used to send phishing emails during times when users are active in order to increase the chances a poisoned link will be clicked.
It sifts through a user's previous tweets using its machine learning capabilities to craft tweets relevant to a target's interests, outpacing previous works that have merely spun Tweeted statements into questions.
Seymour and Tully fed their beast with some two million tweets when testing over a week of processing effort. Of the 90 Twitter users tested, between 30 to 60 percent clicked the phishing links, way above usual click rates.
Only the choicest Twitter victims that represented high value are targeted in order to stay under the radar of defenders employed by the 140 character social network giant.
"Clickthrough rates are among the highest ever reported for a large scale phishing campaign, underscoring the efficacy of coordinated automatic social engineering at scale," the duo say.
Publication of the tool is made in the name of awareness, the pair say, as is much offensive security research. ®
