This article is more than 1 year old
Chinese gambling site served near record-breaking complex DDoS
Nine vectors used as bad guys try to beat defenders.
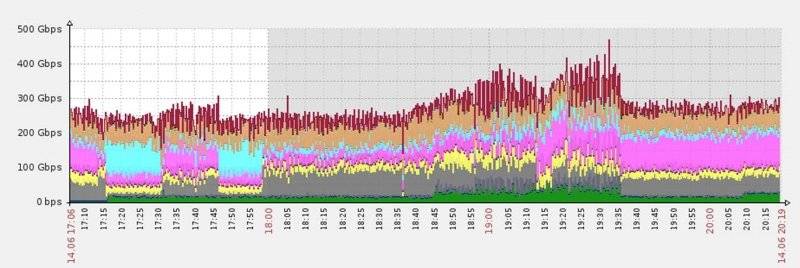
A chinese gambling company has been pulverised with multiple nine-vector, 470 Gbps, 110 million packet-per-second distributed denial of service (DDoS) attacks, some of the biggest and most complex ever recorded.
The unnamed company was attacked by DDoS that used nine vectors in a very rare bid to bypass Incapsula's mitigation services. "The assault was significantly complex by network layer standards, relying on a mix of nine different payload types," Incapsula researchers Ofer Gayer and Igal Zeifman say.
"Such nine-vector assaults are very rare in our experience.
"Usually a perpetrator’s goal in using multi-vector attacks is to switch between different payload types in an attempt to bypass a mitigation service."
The anti-DDoS firm says only 0.2 percent of attacks it saw in the first quarter of this year were multi-vector.
The pair say attackers begun attacking the gambling company with a measly 250Gbps DDoS before stepping it up to launch the heaviest ever recorded by the firm.
Attackers again altered to drop to smaller payloads that would increase assault packet per second rates.
"Using smaller payloads to reach extremely high packet forwarding rates was a common tactic in many large attacks we mitigated this year," the duo say.
"Doing so helps perpetrators max out the processing power of current-gen mitigation appliances—one of their most common weak spots."
Most of the attack traffic was SYN payloads, generic UDP, and TCP.
While the DDoS is large, and possibly the largest to date, the pair say there is not "much difference in mitigating 300, 400, or 500 Gbps" attacks.
"Large attack waves aren’t more dangerous than smaller ones. All you need is a bigger boat."
Gambling companies are regularly smashed by DDoS with some paying ransoms for it to stop as a matter of business. ®