This article is more than 1 year old
And as for actual WordPress pingbacks .... you should probably switch 'em off
Patch adds warning label nobody reads
More than 26,000 WordPress sites have been enslaved and used in a recent distributed denial-of-service attack campaign using a vulnerability first described in March 2014.
The layer seven attacks exploit the pingback feature activated by default on WordPress sites, which informs other sites when they have been linked to. Those pingbacks can be abused to flood sites.
WordPress pushed a fix April 2014 in version 3.9 and later which added IP addresses logs that show the origin of pingbacks, but attackers don't seem to mind.
Sucuri malware analyst Daniel Cid says the attacks represent about 13 per cent of distributed denial of service attacks hitting its customers.
"Despite the potential reduction in value with the IP logging, attackers are still using this technique often enough," Sid says.
"Since the attack is coming from thousands of different IPs, network-based firewalls will do little to stop the attacks as they only do rate limiting per IP address."
Cid says in one case alone, 26,000 WordPress sites were abused to generate a sustained pingback stream of up to 20,000 HTTPS requests per second against one website.
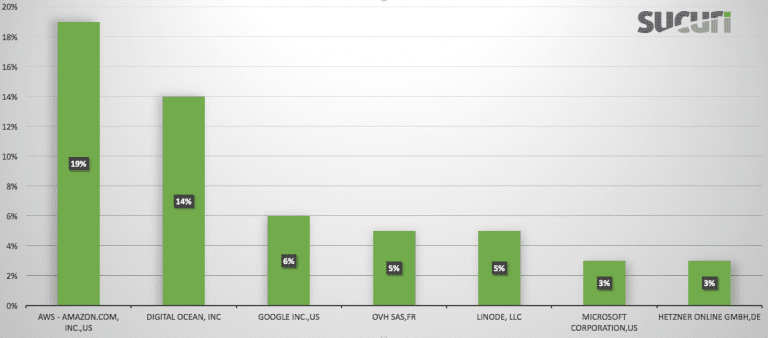
Stats showing attacks originating from various providers.
The attack, which uses more resource-intensive HTTPS, is one that few servers could handle – even with load balancers and proxies in place.
While the IP-address logging patch helps, it is far from a mitigation since few WordPress admins check their user agent logs. Cid recommends the pingback feature be turned off to reduce the resources available to attackers.
In 2014, WordPress pingback attacks included more than 162,000 machines. ®
