This article is more than 1 year old
Cisco drops 11 clock-crashing patches for 46 things, probes 142 more
Borg assimilates NTP January update, nixes critical firewall hijack hole
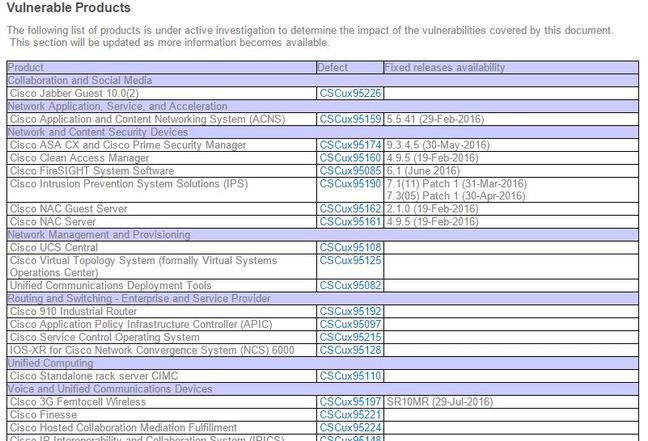
Cisco has patched 11 remote denial-of-service and network time protocol vulnerabilities spanning at least 46 products and is investigating a further 142 offerings which may be affected.
The patch bomb is an ongoing effort to crush the medium-severity CVEs that can allow unauthenticated attackers to mess with NTP servers triggering crashes or altering clocks.
Those 11 bugs were published by the NTP Consortium last week in a disclosure that flew underneath industry radars.
"... versions of [Cisco's Network Time Protocol daemon] package are affected by one or more vulnerabilities that could allow an unauthenticated, remote attacker to create a denial of service condition or modify the time being advertised by a device acting as a network time protocol server," Cisco security wonks say.
"Cisco is currently investigating its product line to determine which products may be affected by these vulnerabilities and the impact on each affected product."
The Borg will assimilate patches over the coming months as vulnerable products are identified.
It says it is not aware of public exploitation but admins should consider it likely that attackers will take advantage of the public disclosure and target the laundry list of exposed networking products from Cisco and other popular vendors yet to apply fixes.
Patch, patch, patch, patch, patch
In a bid to keep admins frowning, Cisco also dropped a patch for a lone critical authentication bypass vulnerability within its RV220W wireless network firewall.
That hole allows unauthenticated remote attackers to gain admin privileges on network boxen thanks to lax input validation of HTTP request headers.
"An unauthenticated, remote attacker could exploit this vulnerability by sending a crafted HTTP request that contains malicious SQL statements to the management interface of a targeted device," the Borg droned.
"Depending on whether remote management is configured for the device, the management interface may use the SQL code in the HTTP request header to determine user privileges for the device. A successful exploit could allow the attacker to bypass authentication on the management interface and gain administrative privileges on the device." ®
