This article is more than 1 year old
Edge joins Explorer in bumper crop of security patches
No zero days but plenty to be getting on with
It's Patch Tuesday the second day of the week in the month of November and Microsoft and Adobe have pushed out their security updates. Joining the perennial favorites Flash and Internet Explorer comes new kid on the block, Edge.
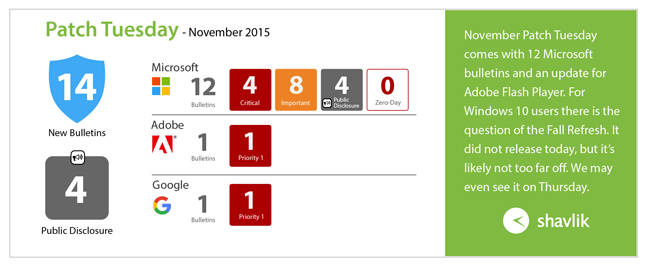
Top line news: no zero days this month but there are four critical updates and eight important ones from Microsoft, four of which cover security holes that have already been publicly revealed, so it's time to get patching.
Most Microsoft updates are for Windows but also Office and Skype (for Business). One (MS15-113) covers the new Edge browser on Windows 10. This will need to be applied after the "fall refresh" for Windows 10, which is expected this Thursday.
As a quick overview, here is a handy graphic from Shavlik.
Those patches in full:
MS15-112. Critical. Remote Code Execution. Internet Explorer. A bundle of fixes; the worst allows for remote code execution giving same rights as user if you visit a specifically designed webpage.
MS15-113. Critical. Remote code execution. Edge. Another bundle. Same problem as 112 above.
MS15-114. Critical. Remote code execution. Windows Journal. Remote code execution if you open a special Journal file.
MS15-115. Critical. Remote code execution. Windows. Opening a special document or visiting a specific webpage (embedded fonts).
MS15-116. Important. Remote code execution. Office. Opening a special file. User-level access.
MS15-117. Important. Increased access level. Windows NDIS. Attacker can increase access level if logged in and able to run a special application.
MS15-118. Important. Increased access level. .NET. Attacker can increase access level if visit specific webpage or open special email.
MS15-119. Important. Increased access level. Winsock.
MS15-120. Important. Denial of Service. Windows. Attacker needs to be logged in but can take server offline.
MS15-121. Important. Spoofing. Schannel. Man-in-the-middle attack.
MS15-122. Important. Bypass security. Kerberos/BitLocker. Attacker needs physical access but could get passed Kerberos authentication and decrypt BitLocker drives.
MS15-123. Important. Info leak. Skype for Business. Inviting target to IM session can cause an information leak through Javascript insertion.
Adobe
As usual, there are plenty of Flash updates: 17 in fact. Many are "priority 1," which means patch them as soon as possible. And expect some plug-in updates as a result for IE, Firefox, and Chrome.
The holes could allow an attacker to take control of the affected system. The CVE-listed vulnerabilities are: CVE-2015… 7651 to 7663 and 8042 to 8046. ®
