This article is more than 1 year old
Hackers can steal your BRAIN WAVES
Depressingly familiar and stupid mistakes in EEG kit, health org's storage of recorded brains
BruCon: Behold the future: attackers can already get between brain-waves and hospital kit, and it's just going to get worse according to IOActive senior consultant Alejandro Hernández.
Hernández says the ability to steal, manipulate, and replay brain waves used in electroencephalography (EEG) is already emerging, with consumer-grade kit already able to be hacked and the health care industry taking few precautions to properly protect recorded brain waves.
After decades in labs and hospitals, encephalography is steadily being implemented in lightweight consumer headsets and other devices that as yet remain largely experimental or gimmicky.
In clinical settings, EEG-recording devices are a useful tool for diagnosing seizures and sleeping disorders like narcolepsy.
Researchers think recorded brain waves have the potential to score the mental faculties of murderers, create brain-to-brain interfaces where conscious thoughts are transmitted over the internet and unconsciously enacted by another person or see drones flown by neural impulses.
Before we get there, we'll need to lock down EEG devices. Hernández says a year's research taught him how to find discover holes in EEG equipment and come to the recognition that recorded brain waves should be considered sensitive data and therefore encrypted. The researcher worked with a US$80 MindWave device
pitched as a tool to help measure how students' brains work when doing maths and other problems.
Hospital-grade machinery remains out of reach of hackers without deep pockets and the required intricate knowledge of which brain waves can be modified for a given outcome.
Nevertheless, Hernández asserts that dangerous vulnerabilities exist in home and likely hospital kit, including data stream stealing and application holes, and garden-variety man-in-the-middle and denial-of-service attacks.
The required knowledge too is not exotic or unobtainable for a determined hacker.
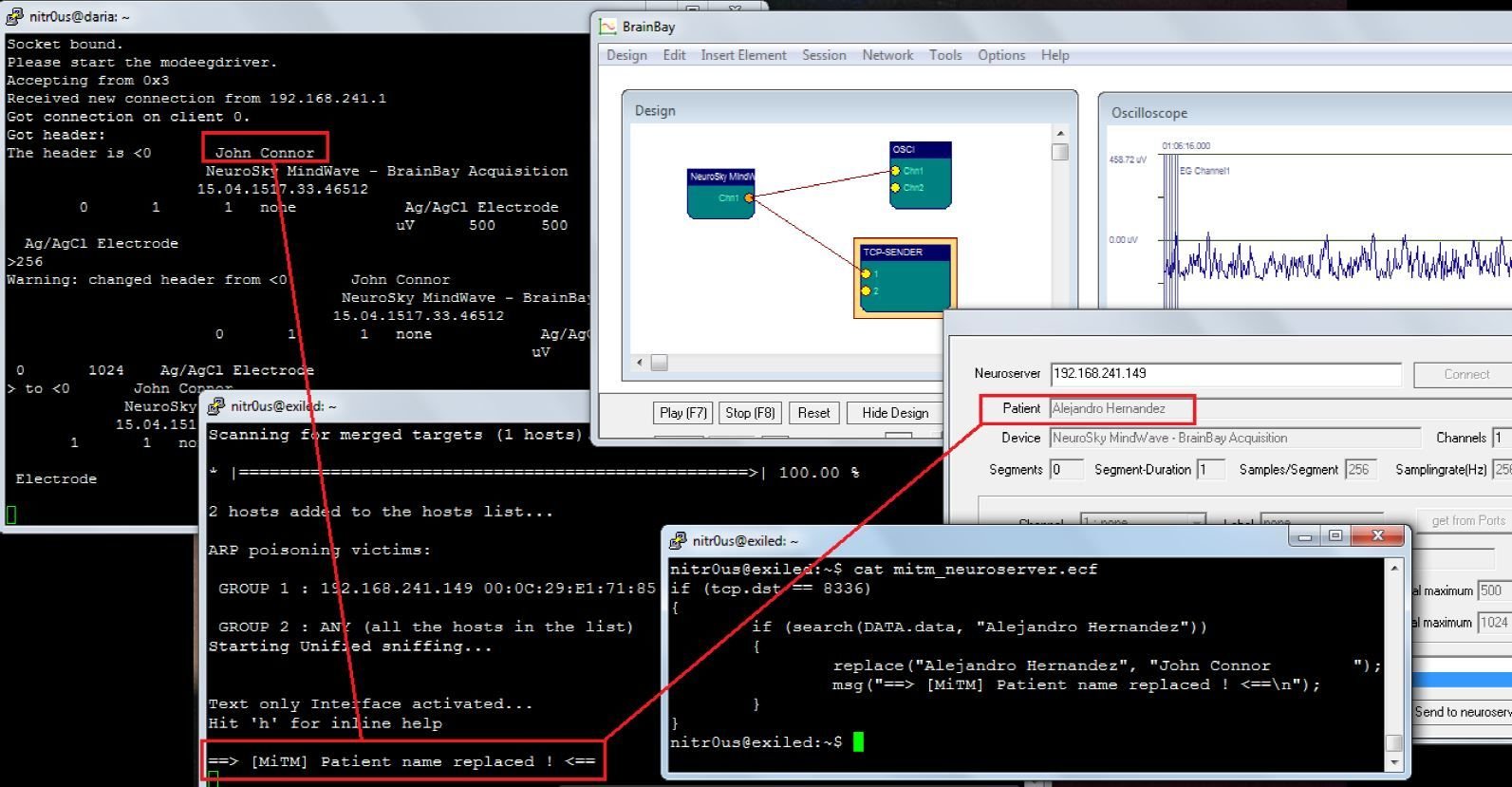
The hacker demonstrated at the BruCon conference last week a live man-in-the-middle attack on his own brain signals using the unsupported but still very widely used open-source EEG NeuroServer package.
“Years ago no-one was worried about SCADA networks just that it works, and a decade later we are talking about [SCADA] security… I am finding exactly the same thing with EEG and now is the best time to put security in the technology,” Hernández told the conference.
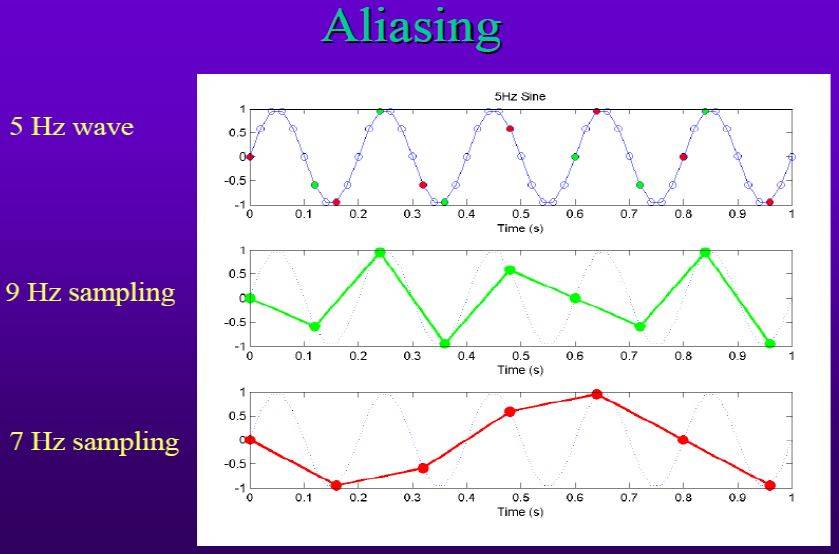
“If you can sniff brain data in the wire, you can do replay attacks [such as] if there is no security mechanism between an operator and a drone [or by] tampering with EEG data so it is not the same that was recorded by the electrodes.
“Or how about instead of spammers, there are EEG data neural marketers?”
EEG data also poses more prosaic risks. Hernández told Vulture South of an un-named hospital's EEG file shares, saying the server could be found exposed by using the popular Shodan hacker search engine.
These attacks are part speculation, part tested, but all built on the evidence that EEG like so many emergent technology fields has left security in the dust of capability progress. Hernández has however popped the mental locks of popular gear within the realms of the everyday hacker.
Mind bending
EEG's security problems are depressingly familiar results of bad software design, Hernández told this reporter. The ENOBIO EEG device (which rather resembles rugby headgear) is vulnerable to man-in-the-middle attacks. He found less-severe application vulnerabilities and ordinary crashes in EEG software including Persyst Advanced Review; Natus Stellate Harmonie Viewer; NeuroServer; BrainBay, and SigViewer.
“For example, some applications send the raw brain waves to another remote endpoint using the TCP/IP protocol, that by design doesn’t include security, and therefore this kind of traffic is prone to common network attacks such as man-in-the-middle where an attacker would be able to intercept and modify the EEG data sent,” Hernández says.
Further, components like the acquisition device, middleware, and endpoints lack authentication meaning an attacker can connect to a remote TCP port and steal raw EEG data. That same flaw lets attacks pull off the more dangerous reply attacks.
Hernández cannot speak for the state of security of hospital-grade EEG kit, which is harder for hackers to access and test. But his research is bad news for those who advocate EEG readings as an authentication mechanism.
The good news, the researcher says, is that the vulnerabilities he's found can be nixed with known best practices: “This is a big yes – best practices from the technology perspective, secure design, and secure programming should be followed”. ®