This article is more than 1 year old
Porsche-gate: Android Auto isn't slurping tons of engine data, claims Google – but questions remain
Just how much can the app access?
Google has flatly denied that its Android Auto car dashboard software slurps too much information from vehicle engines.
It was earlier claimed that Porsche snubbed the system because it was shocked by the alleged data gobble.
Google convinced many automotive manufacturers to use Android Auto for their in-car entertainment and information systems, but Porsche went with Apple and iOS instead. According to a report in Motor Trend, Porsche snubbed Google because the advertising giant's software wanted vehicle speed, throttle position, coolant and oil temperatures, and engine revs.
A source told the petrolhead mag that the German automaker wasn't happy handing over these diagnostics to a company that is potentially a rival – once computer-controlled robo-cars are allowed on the streets, of course. But Google told El Reg that the story isn't true.
"We take privacy very seriously and do not collect the data the Motor Trend article claims such as throttle position, oil temp, and coolant temp," the California biz said in a statement on Wednesday.
"Users opt in to share information with Android Auto that improves their experience, so the system can be hands-free when in Drive, and provide more accurate navigation through the car's GPS."
(It's possible Porsche dumped Android Auto because Apple's brand is a better match for the automaker's flash motors.)
Data slurping from engines: what's the big deal with Android Auto
Android Auto does monitor some data from the engine. The software checks to see if the car is moving, for example. It can access GPS, steering-wheel controls, the sound system, and wheel speed, in fact.
Don't forget that Android Auto isn't the car's firmware – it's really just an app running on a smartphone, which is connected by USB to a dashboard display. The phone does all the work in rendering maps, playing music, and so on, using the dashboard as a second touchscreen and the audio system as external speakers. Android Auto also listens out for voice commands to take instructions from the driver and passengers. (Commands such as play the next album, or which way to the store, not slam on the brakes.)
That dashboard hardware links either directly or indirectly the phone to the vehicle's CAN bus, which is its central nervous system. This is the network that the engine control unit, the airbags, the power train, the antilock braking system, the electric power steering, and other vital hardware share to pass around information. CAN was not designed with any security in mind – any controller on the two-wire bus can access another.
So two things spring to mind: one, what exactly is stopping Android Auto from slurping lots and lots of different types of data – from engine revs to oil temperature – from the CAN bus? Is the app programmed to play nice, or is there a physical defense? Here's an ideal setup:
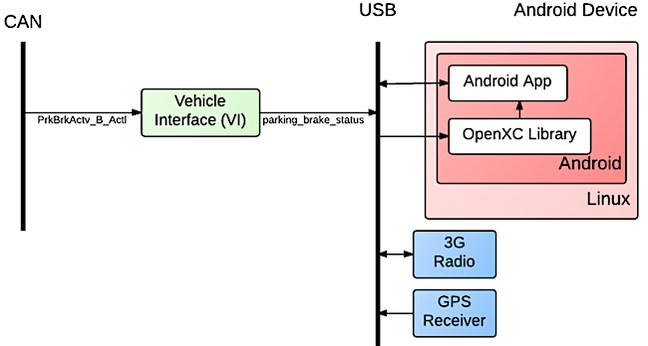
Do the CAN can ... How the OpenXC platform organizes Android and the CAN bus
In the above case, from the OpenXC platform, the Android device can be firewalled off from the critical CAN bus by a suitable CAN-to-USB translator; the Android gadget can only request information, such as wheel speed or whether the parking brake is on.
That gateway could block requests for low-level statistics that manufacturers and drivers would rather keep private. But if that gateway honors any request for data, we're relying on Google keeping to its word and programming Android Auto to only fetch limited types of information.
Cars these days have OBD-2 diagnostic ports that allow plugged-in devices to query anything on the CAN bus – is this the case for Android Auto, too?
The second thing that springs to mind is: can the connected smartphone write to the CAN bus as well as read from it? If the device is completely compromised in some way – such as by malware exploiting Stagefright bugs – can it fire commands into the vehicle's brain stem? Android Auto needs to be able to control the audio system to pump up the volume or turn it down, for example, and if that means it writes to the CAN bus to do so, then any mayhem can be caused by the phone.
Perhaps the cars compatible with Android Auto have compartmentalized CAN buses so the audio system is blocked by a gateway from the engine control hardware – although reprogramming controllers on the bus to bypass these defenses is possible. Most controllers are extremely simple with little security, and pushing past them can be trivial.
We note that Chrysler didn't have much in the way of compartmentalized in its its hacker-vulnerable rides.
Perhaps the audio systems are controlled without CAN bus access: the dashboard could connect the phone to the radio and speakers via a separate media-only network, so the Android Auto app can direct sound around the vehicle without getting close to safety-critical systems.
We haven't been able to get a straight answer from Google on this.
We can only hope the dashboard, or head unit, acts as a broker between Android Auto and the CAN bus, allowing some data to be read from the machinery, and controlling the audio systems through a non-critical secondary network.
Here's my updated system for protecting driver privacy and vehicle security when connecting devices to the CAN bus: pic.twitter.com/hQLYrqrW7z
— Ken Tindell (@kentindell) October 8, 2015
Google has convinced nearly 40 automakers to look at Android Auto. Hyundai was first off the block, with cars using the software rolling off the production line in May. ®
