This article is more than 1 year old
The last post: Building your own mail server, Part 3
Adding some much-needed spam and virus filtering
Other useful tweaks
There are lots of tweaks you can make to a system like this - it's probably impossible to give a definitive config.
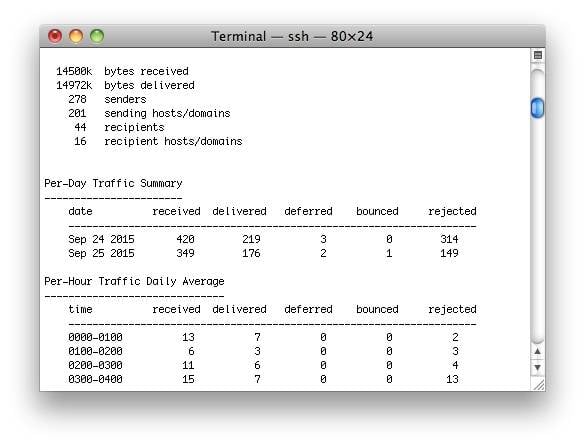
You can use pflogsumm and other tools to help monitor your mailserver
At the moment, I'm testing the use of the built in Postfix postscreen daemon, which can do some simple checks on inbound connections. I've set it up to check against Spamhaus and Barracuda blocklists, dropping connections if they're listed. It then passes on to the rest of the setup - first Postgrey and then Amavis. Postscreen can, effectively, greylist on its own, but it was simplest to drop it in as a first stage defence.
For backup of user emails, you can install a package like duplicity, which can do incremental backups, using rsync or even to services like Amazon S3. So, this script will do an incremental backup, and a full backup every two months, of all files in /home. Just add it to /etc/weekly.local to schedule it one a week.
ulimit -n 1024 RSYNC_PASSWORD=bigFatSecret duplicity --no-encryption --full-if-older-than 2M /home rsync://backup@some.rsync.server::/path/folder
If you want to be able to create and delete addresses easily, for example to give one to each company you deal with, it's easy to use a database as well as the text file. Change the setting for virtual_alias_maps in main.cf to
virtual_alias_maps = hash:/etc/postfix/virtual_alias, mysql:/etc/postfix/maildb.cf
Then create the a file called maildb.cf to say which database and query is used to map an alias to a destination
# alias table for itpa email system hosts = some.mysql.server user = myMySQLuser password = myMySQLpassword dbname = alias_database table = aliases select_field = destination where_field = aliasname
Then, you could create an alias in MySQL with something like
INSERT INTO aliases ( aliasname, destination ) VALUES ( 'register@nigelwhitfield.com','nwmail') ;
And with that, we're more or less done. So, it's over to you - for more comments, tips and suggestions. ®
