This article is more than 1 year old
Intel left a fascinating security flaw in its chips for 16 years – here's how to exploit it
Howler opens door for SMM rootkits
Black Hat In-Depth A design flaw in Intel's processors can be exploited to install malware beneath operating systems and antivirus – making it tough to detect and remove.
"It's a forgotten patch to a forgotten problem, but opens up an incredible vulnerability," said Christopher Domas, a security researcher with the Battelle Memorial Institute, who revealed the hardware bug at the Black Hat conference in Vegas last week.
The blunder was introduced in 1995, in the Pentium Pro. It is hardwired into the silicon, and has been staring kernel-level programmers in the face for years.
It allows smart hackers to run rootkit code at the very lowest level on the computer, out of reach of the operating system, its applications, and even the hypervisor. This means the rootkit can, among other things, silently monitor and record the user's every keypress, mouse click, and download.
Efforts to detect the rootkit and eradicate it from a computer can be blocked, or hampered, by the malware itself. A nightmare, in other words.
The good news is that Intel spotted the howler in its processor blueprints, and corrected the issue: chips built from January 2011 and onwards (Sandy Bridge Core CPUs and later) are not affected. Also, operating systems can mitigate against the security hole at the hypervisor level, thus protecting themselves from miscreants exploiting the design flaw, according to infosec boffin Jacob Torrey.
Domas reckons there are hundreds of millions of Intel processors permanently vulnerable – they cannot be updated to fix the problem.
A trusty Linux box from the previous decade that's still plodding away, an office of old PCs, or a relative's aging laptop, are the sorts of computers at risk of attack via this vulnerability. Your fancy new gaming rig, your virtual machine in the cloud or on your workstation, and that office PC bought two years ago in the last refresh, are immune.
The design flaw is super-interesting. Even though today's chips do not feature the engineering gaffe, it's worth studying so lessons can be learned. Essentially, it is possible to execute arbitrary code in the processor's all-powerful, and normally locked away, System Management Mode by abusing an obscure feature in the CPU, and we'll explain what that means.
Layers! Onions have layers. Computers have layers
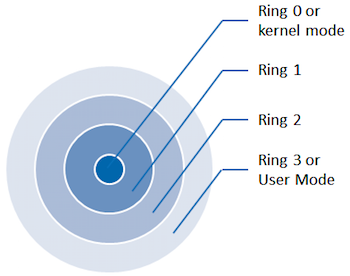
Intel-compatible processors separate software into what's called rings of privilege, or rings of protection. Lower rings manipulate and control the upper rings, and the upper rings are forbidden from interfering with the lower rings.
Normal applications run in the uppermost unprivileged ring, aka ring 3, and they can't directly affect the underlying system. Ignore rings 2 and 1; virtually nobody uses them.
Your operating system runs in ring 0. Apps in ring 3 cannot directly meddle with the OS and compromise it because the OS is protected in ring 0.
Then there's ring -1, which is where the hypervisor lives, if you're using one. The hypervisor looks after one or more operating systems that live in ring 0. The hypervisor, being in ring -1, is protected from the operating systems running in ring 0. This stops a guest operating system from taking over the host machine.
Your PC's hidden creepy janitor
Finally, under all that, there's ring -2, which contains Intel's System Management Mode (SMM) software. This is untouchable from all the other rings, and is loaded from the motherboard firmware before any operating system or hypervisor is started. The SMM works invisible to the other rings. It is like a hidden creepy janitor, doing little background jobs and keeping the hardware ticking over without the other rings realizing.
For example, the SMM code controls the power to the motherboard hardware when the user wants to put her computer to sleep or wake it up. It emulates a PS/2 keyboard when only a USB one is plugged in. It quietly deals with chipset errata – in other words, if an operating system or hypervisor attempts to access buggy motherboard hardware, the SMM will intercept the request and make it all work as expected in software.
All this happens transparently to the other rings: code running in SMM is invisible to the rest of the computer, and it has complete control over the hardware and firmware. It is the real sysadmin of your PC. Taking control of this janitor means taking control of everything.
Where the janitor lives and works
The SMM code reserves a small chunk of your PC's RAM to store its variables and other private data, and all other rings are forbidden by the motherboard hardware from accessing it. That chunk starts at 0x1FF80000, or half way between the 511MB and 512MB marks in your physical RAM. Any attempt to access that portion of memory from software running outside the SMM is blocked by the Memory Controller Hub on your motherboard.
