This article is more than 1 year old
DDoSers call 1988 and want its routing protocol hacked
500 routers whip up colossal DDOS over ye olde RIP protocol
Attackers are exploiting an ancient networking protocol to enslave small home and office routers in distributed denial of service attacks, Akamai says.
The May attacks, described in a report by the global networking company, exploit routers operating version one of the Routing Information Protocol (RIP) developed in 1988 and superseded by version two in 1996.
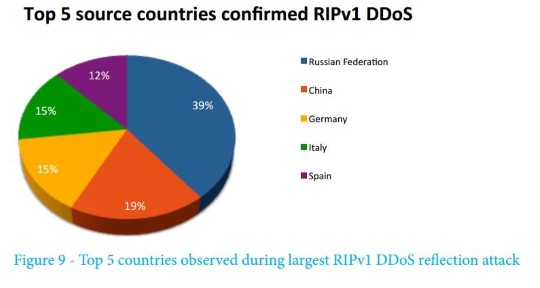
Net pests are generating 12.8Gbps DDoS attacks from some 500 enslaved routers, but have the potential to scale upwards if they target more of the 24,212 exposed devices found vulnerable, Akamai's PLXsert unit says.
"PLXsert has been monitoring an uptick in a form of DDoS reflection previously thought of as mostly abandoned," the report (PDF) says.
"This attack vector, which involves the use of an outdated routing protocol in RIPv1, began showing up in active campaigns again on May 16th after being dormant for more than a year.
"... there is little reason for RIPv1 to continue as an available resource for DDoS attacks. Most of these sources appear to be from outdated hardware that has been running in home or small-office networks for years."
Attackers are able to conceal the source identity by spoofing IP addresses in reflection attacks where exposed routers receive requests from one source but direct it at another.
They can also amplify the attacks by causing routers to respond to requests directed at victims with larger payloads of up to 512 bytes for every 24 byte query.
Most of the dust-covered workhorse routers are Netopia 3000 and 2000 models distributed by AT&T.
Akamai recommends system administrators restrict traffic on UDP port 520 and users to upgrade to RIP version two.
The DDoS attacks are more novel than dangerous. Crims have pushed attacks through Network Timing Protocol amplification that, in 2013, slammed Hong Kong with a 400Gbps traffic deluge.
Net pests have however proved they will take whatever they can get and have used video recorders and other low-powered embedded devices for denial of service and bitcoin mining. ®
