This article is more than 1 year old
Rivalry heats up as VXers bake Fobber crypto clobber
Hop, skip, and headache.
A malware development squad is so determined to thwart meddling white hat researchers that it has produced a trojan riddled with obfuscation techniques and neurotic encryption.
The Fobber banking trojan is based off Tinba version two, regularly hops between programs, and is distributed through the elusive and dangerous HanJuan exploit kit.
Malwarebytes researcher Jerome Segura says the authors have encrypted command and control communications, and each separate small code function, making reverse engineering a formidable task.
"The samples we have observed always attempt to open random registry keys and then the malware performs a long sequence of jumps in an effort to create something like a rabbit hole for analysts to follow, slowing down analysis," Segura says .
"The dropped binary, which we nicknamed Fobber, has the ability to steal valuable user credentials and is also fairly resistant to removal by receiving updates to both itself and command servers.
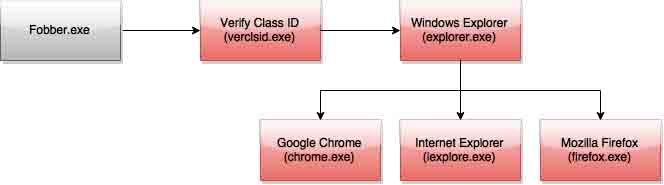
"Unlike a normal Windows program, Fobber makes it a habit to “hop” between different programs."
Segura says the authors are "testing the waters" with the malware before distributing it more widely. The white hat's analysis would doubtless infuriate the cautious criminal coders.
He says the malware is flogged through a noisy malvertising campaign which is out-of-place for the handiwork of the stealthy HanJuan exploit kit, unknown prior to late last year and normally restricted to high-value and zero-day attacks.
Equally anomalous is the use of a genuine hacked Joomla! site for hosting HanJuan, a fact that Segura has exploited by requesting the hosting provider for further forensic analysis.
"Every encounter with HanJuan is interesting because it happens so rarely. As always the exploit kit only targets the pieces of software that have the highest return on investment: Internet Explorer and [Adobe] Flash Player," he says.
Fobber throws a further fork in the analysis wheels by eschewing traditional methods of process watching.
Instead it creates a kind of checksum value derived from process names of Windows processes including Chrome, Internet Explorer and Firefox, which is then matched against hard-coded process checksums. ®