This article is more than 1 year old
Spooks BUSTED: 27,000 profiles reveal new intel ops, home addresses
Searchable OPSEC built by scouring LinkedIn for folks claiming spook skillz
A trio of transparency boffins have revealed personal details of 27,000 intelligence officers they say are working on surveillance programs. The resulting dump not only names the officers, but in some cases tells you where they live based on data sourced from LinkedIn profiles and other easy-to-access sources.
M.C McGrath, founder of Transparency Toolkit, along with coder Brennan Novak and sysadmin Kevin Gallagher have compiled the records into the ICWatch database searchable by company, title, name, and location.
McGrath says the astonishing open-air intelligence gaffes reveal details about intelligence officers' private and work lives, along with previously unknown intelligence programs.
"Luckily it is very easy to find out who is in the surveillance state with just a few Google searches," McGrath says.
"People post things like 'I know how to use XKeyScore and MS Word'."
McGrath speaking at the Re:Publica conference in Berlin this week identifies four spooks and used easily-accessible data on LinkedIn, Facebook and other sites to rebuild their personal and work lives.
One blundering spook listed working on more than two dozen surveillance programs including XKeyscore, WealthyCulster, and PinWhale, along with new surveillance programs not currently on the public record.
McGrath is able to infer basic definitions of those new codewords based on the context provided on LinkedIn profiles.
"[One spook] identified, collected, and performed direction finding of specific target signals using PENNANTRACE, DISPLAYVIEW and CEGS and it looks like something around geo-location data and airborne SIGINT platforms, so potentially something with SIGINT drones."
The spook chaser then probed other online resume sources to learn more about the PENNANTRACE and intel programs. He found one veteran of some 22 years appeared to have lobbied for "transparency and change" concerning some intelligence programs, swapping jobs within months, before quitting the industry and becoming a used car salesman.
"It's an indication that people are perhaps trying to change the intelligence community from within," McGrath says.
The ICSWatch database, offline at the time of writing, is compiled from LinkedIn searchers for industry terms including OSINT, SIGNIT, and TSSCI.
The Register has inquired about the cause of the outage.
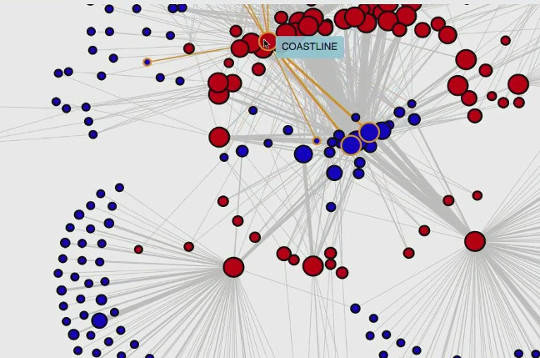
The activist team has also created active network graph visualisations showing which companies and LinkedIn members work with which programs, and the relationships between the military and surveillance industries.
That graph data is based on a LinkedIn feature which shows related profiles.
They also mapped the number of mentions for specific programs over time, possibly indicating the commencement of large programs and the agencies involved.
He says open source data sources will continue to crop up even if those exposed in the current work are shut down, and notes that the data should not be used to demonise those in the intelligence industry.
"I'm hoping this data will be used to start debates about programs not previously known .... or to use this information as the basis for FOI (freedom of information) requests".
McGrath says the irony of blundering spooks listing OPSEC as a skill is not lost on him.
He invites interested and capable people to get involved in the project.
The database is available on GitHub. ®