This article is more than 1 year old
CloudFlare launches nameserver DDoS shield
Hosed and hapless hosters to hide from hackers
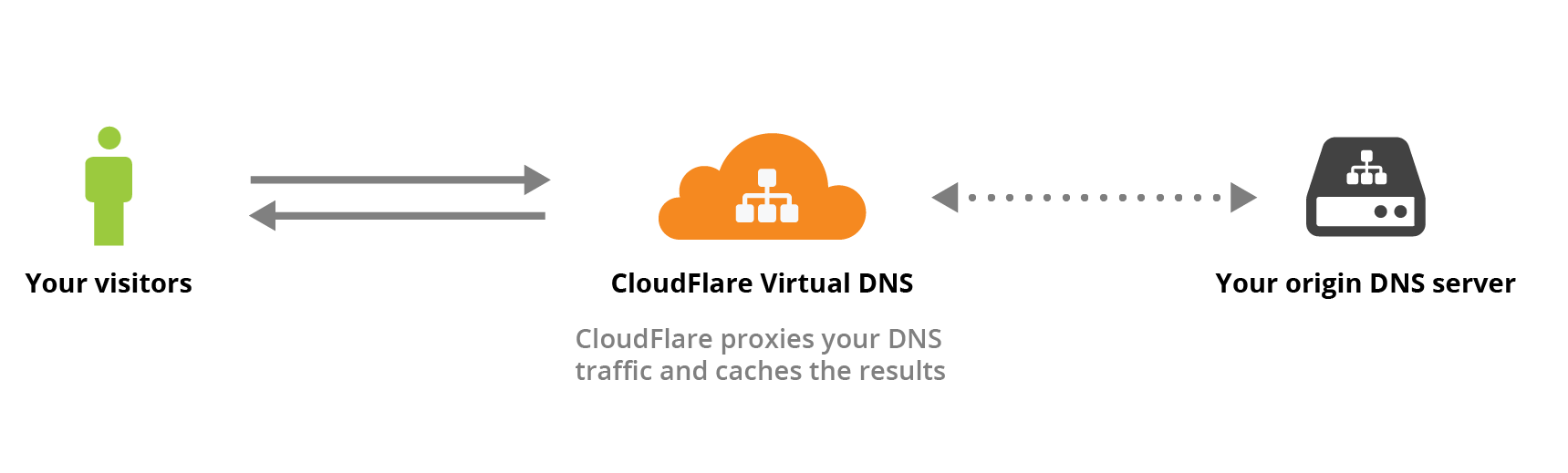
CloudFlare has launched a DNS proxy service it says will help organisations improve DNS resilience by pushing distributed denial of service attacks to the outer edge of its network.
The Virtual DNS service is billed as a means for DNS providers to mitigate a potential "massive single point of failure" in their nameservers caused by legacy IT infrastructure.
CloudFlare engineer Dani Grant says the service will act as a domain authority for nameservers.
"With Virtual DNS, DNS queries for the provider's records are responded to by the nearest CloudFlare edge location [and] if the proper DNS response is available in CloudFlare's cache, CloudFlare will return the response to the visitor, saving bandwidth at the origin nameserver," Grant says in a post.
"If the DNS response is not available in cache, CloudFlare will query one of the provider's nameservers in the background to fetch the DNS response and send it back to the visitor.
"To protect against attacks, malicious requests to the nameservers will be identified and blocked at CloudFlare’s edge before those requests ever make it to the provider's DNS infrastructure."
Grant says hosting providers often have stubborn legacy DNS infrastructure that lacks the security chops required for potentially thousands of clients that are provided nameservers.
The service will mask IP addresses of a provider's nameservers and continue to answer DNS requests from its cache in the event the servers are knocked offline.
She says the service has been tested over the last year and is being rolled out to enterprise customers.
New York-based virtual private server mob DigitalOcean signed on as an early customer in July and is now delivering 10,000 requests a second, according to Grant, without malicious traffic having hit its nameservers.
The project comes after the DDoS deflection platform in February deployed faster cipher suites to improve browsing on fondleslabs.
Late last year the company finished a two-year effort to switch on keyless SSL that let customers encrypt web traffic through its services without having to hand over private SSL keys. ®
