This article is more than 1 year old
Attackers sling recent Flash 0day through 1800 domains
Nuke it from orbit. It's the only way to be sure
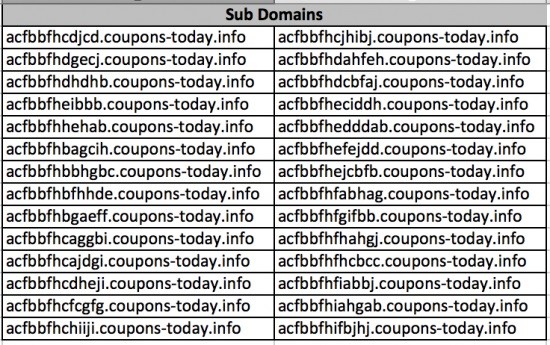
Some 1800 subdomains have been found slinging the Angler exploit kit using Adobe's most recent Flash zero day exploit, Cisco researcher Nick Biasini says.
The lion's share of nasty subdomains were set up on 28 and 29 January and tied to about 50 GoDaddy registrant accounts.
Biasini said the malvertising attacks used several layers of subdomains to avoid detection.
"Researchers detected the new campaign when referencing a known hash that was delivering the recent Flash zero day (CVE-2015-0311)," Biasini said in a post.
"These domains are associated with the landing page and exploits [and] none of the actual root domains appear to be compromised and are legitimately registered to owners.
"It appears that the actors have managed to compromise a large group of registrant accounts and have set up subdomains ... some of them are only seen once before being abandoned."
Some of those compromised accounts held more than 45 domains making them ripe targets.
About 650 subdomains were used as redirection pages tied to a single IP address which then delivered victims to malicious landing pages which would serve the exploit kit.
The exploit kit also served Microsoft Silverlight exploits targeting vulnerabilities patched earlier last year.
Adobe has fought off a trio of recent zero day vulnerabilities, some first discovered under active attack in recent weeks.
Trend Micro threat analyst Peter Pi said it detected Monday 3294 hits tied to the most recent unpatched exploit in yet more malvertising attacks. ®