This article is more than 1 year old
Knock Knock tool makes a joke of Mac AV
Yes, we know Macs 'don't get viruses', but when they do this code'll spot 'em
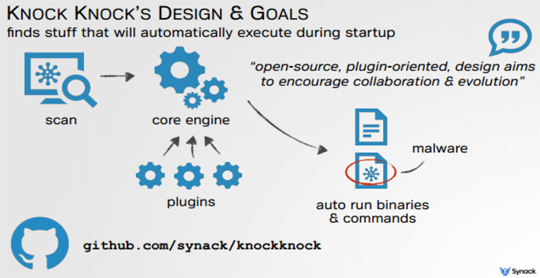
Security research and development bod Patrick Wardle has released a tool to reveal executables that automatically boot in Mac OS X.
The Knock Knock tool was open source and built on an extensible framework to encourage the community to evolve the platform.
Wardle, of consultancy Synack, said he designed the tool because he was concerned about the lack of insight into the potential for persistent malware to load on his machine, a worry justified he said given Apple's "feeble" anti-virus protection and that a further 33 OS X malware families were discovered last year.
"I was really bothered by the fact that I did not know what was automatically executing on my computer or if there was any persistent malware on my computer that I wouldn't know about it," Wardle said.
"[Knock Knock] should show me everything that is set to automatically execute when my Mac is rebooted.
"I've run it on some friends' computers and actually found a bunch of OS X malware."
Knock Knock
He added that a fully patched Mac was "not that secure" and that the built-in anti-malware mechanisms were "pretty lame".
"There [are] tonnes of ways for malware to persist on OS X and Mac malware is certainly a reality, particularly if you're a Chinese activist or one of my friends who I guess have questionable browsing habits."
In one example it detected the "clipboardd" persistent malware when it listed all binaries unsigned by Apple meaning users needed to have knowledge of OS X malware.
Plugins could be added to scan for new persistence techniques to keep it abreast of threats.
Wardle said writing the plugins was simple and noted the beta-phase command line tool was stable and usable. ®
