This article is more than 1 year old
Roll your own Bitcoin client? Prepare to be raided
Attackers exploit borked random numbers
The engineer behind the Heartbleed checker has created a tool to hunt down wallets from poorly secured transactions that leak private keys.
Filippo Valsorda released the Blockchainer tool to Github following a presentation at the Hack in the Box conference in Malaysia today.
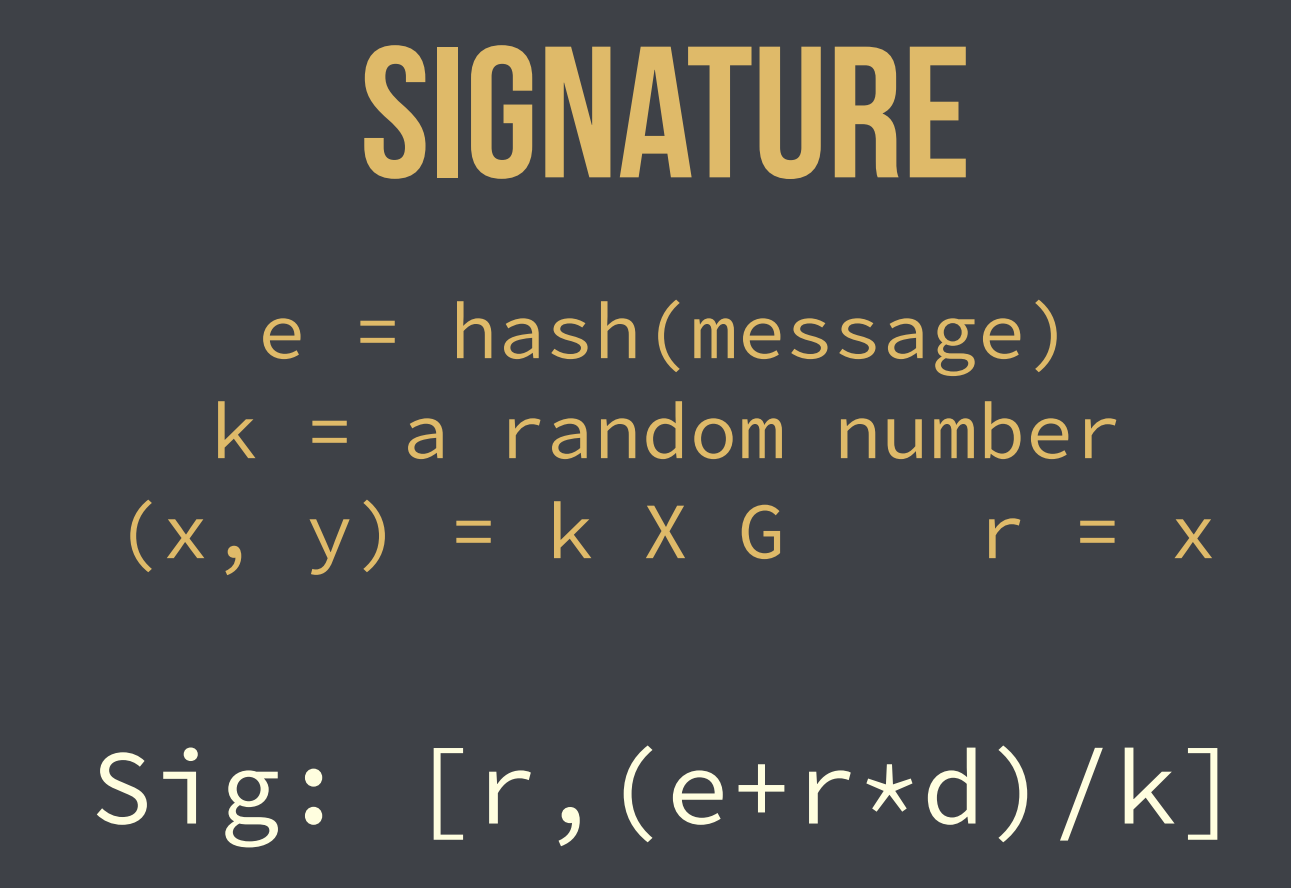
The CloudFlare engineer demonstrated how known flaws in some implementations of the Elliptic Curve Digital Signature Algorithm (ECDSA) have allowed thieves to steal Bitcoins due to factors such as insecure clients or flaws in unpatched browsers.
"I applied a known attack to the real world and showed how you could use ECDSA in a safe way that doesn't need random numbers so that it would not fail scanning the blockchain," Valsorda told Vulture South via Skype.
"I found two really big events where someone probably made an error while writing their client that generated hundreds and hundreds of vulnerable transactions.

"I was able to identify one attacker who stole something like 59 Bitcoins ... targeted the users' browsers that were likely not providing the right random numbers."
That attack happened in August 2013 and was wrongly pinned on Google, he said. Valsorda found some indications that other attackers were scanning and raiding wallets judging by transactions, but could not be conclusive.
"In the research I went over the blockchain to look for mistakes, but the moral was that we should make decisions that by default protect [transactions] when something else fails," he said, adding that the random number should be secret and unique but not necessarily random.
Bitcoin clients Multibit and Electrum received five stars for the correct use of ECDSA, while blockchain.info did not – since it relied on the browser's random number generator.
He stressed this was not a vulnerability in blockchain.info, but rather in the reliance on what could be an unpatched and outdated browser.
Valsorda's tool would scrape for vulnerable Bitcoin transactions and to that end would be helpful to the research community. The researcher found no remaining wallets for raiding and pointed out that attackers could already target those exposed without his script.
"Whoever is developing software has responsibility to users who do not know enough to protect themselves," he said.
His slide deck can be perused here (PDF). ®