This article is more than 1 year old
VMWare virtually in control of Shellshock
Patch here, here, here ... everywhere, really
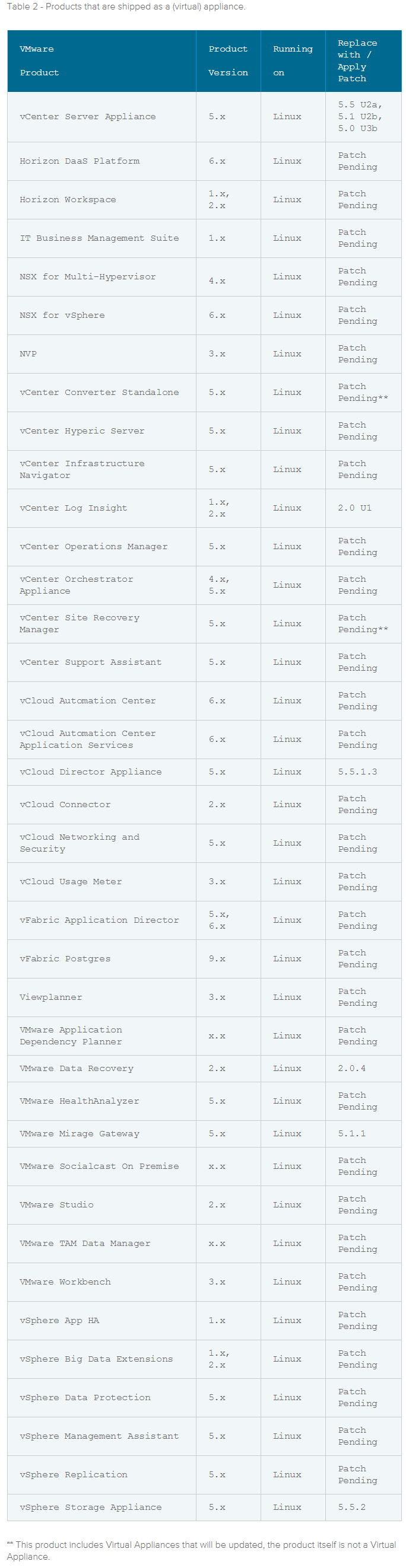
VMware is plugging away at Shellshock holes in 37 virtual appliance products, but has so far shipped clean code for just a handful of appliances.
The company released a fix for cloud analytics kit vCenter Log Insight and offered updates on four others.
The advisory said a variety of VMware appliances shipped with Shellshock-vulnerable Bash.
Products running on Linux, Android, OSX and iOS could inherit the underlying vulnerability of their OS, and VMWare urges customers to contact their operating system vendor for a patch.
ESX variant ESXi is unaffected as it uses the Ash shell, while Windows products including vCentre Server are also unaffected clear.
Affected products also include various versions of vCloud Director Appliance; VMware Data Recovery; VMware Mirage Gateway, and vSphere Storage Appliance.
"VMware encourages restricting access to appliances through firewall rules and other network layer controls to only trusted IP addresses. This measure will greatly reduce any risk to these appliances," VMware said.
The Shellshock Bash bug has triggered a string of patches across affected product vendors. Linux vendors, Apple and OpenVPN have released or were in stages of issuing Shellshock patches.
Rapid7 security researcher Greg Wiseman warned that Apple's patch, like others, may have failed to close off the Shellshock hole.
Wiseman said Apple's patch for Shellshock bugs in 10.8 Mountain Lion didn't close off the hole according to tests run with a bash check tool.
"I ran this on a patched version of 10.8 and verified the fix addresses the first two vulnerabilities, but it seems that the updated version of bash may still be vulnerable to CVE-2014-7186," Wiseman said. ®