This article is more than 1 year old
Cryptome.org hacked to dish out malware
Compromised whistle-blowing HQ begins site rebuild
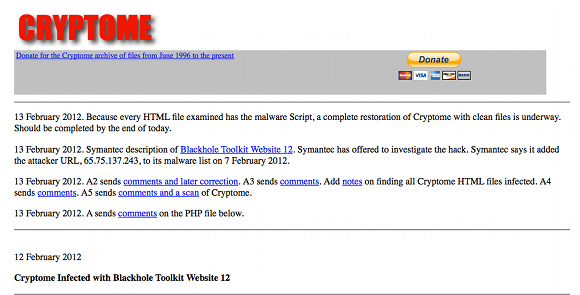
Cybercrooks have planted malicious scripts on top of whistle-blowing nerve centre Cryptome.org.
The website this morning...
The attack, which used the well-known Blackhole toolkit, exposed surfers visiting any page of Cryptome.org to a hacker-controlled page that leveraged browser exploits and the like to compromise readers' machines.
The methods used to breach Cryptome and plant malicious code remain unclear as of Tuesday morning. There are several possible routes to compromise a system, from SQL injections to exploiting a flaw in an public-facing server. It's unclear who carried out the attack or their motives, which might be just to infect machines and plant Trojans as part of a money-making scam or something more targeted against Cryptome's user base.
Cryptome specialises in publishing information about cryptography, surveillance, freedom of speech and related issues. The site has a similar profile to WikiLeaks in some ways, but has been operating for far longer, since 1996.
The whistle-blowing site confirmed the hack and published a notice on its site on Tuesday saying that a "complete restoration of Cryptome with clean files is underway". The restoration process is expected to take around a day. ®
