This article is more than 1 year old
DNS cache poisonings foist malware attacks on Brazilians
'Desperate cries' from those visiting innocent sites
An attack on several Brazilian ISPs has exposed large numbers of their subscribers to malware attacks when they attempt to visit Hotmail, Gmail, and other trusted websites, security researchers have warned.
The attacks work by poisoning the domain name system cache that the service providers use to translate domain names such as google.com into internet protocol numbers such as 74.125.224.144. By replacing legitimate IP addresses with ones leading to servers controlled by attackers, the hack is causing end users to be surreptitiously directed to sites that exploit software vulnerabilities on their computers or trick them into installing malware.
“Last week, Brazil's web forums were alive with desperate cries for help from users who faced malicious redirections when trying to access websites such as YouTube, Gmail and Hotmail, as well as local market leaders including Uol, Terra and Globo,” Fabio Assolini, a researcher with antivirus provider Kaspersky Labs, wrote in a blog post published on Monday. “In all cases, users were asked to run a malicious file as soon as the website opened.”
Assolini said the browser of one machine Kaspersky researchers tested displayed a warning when opening www.google.com.br instructing them to install a program called Google Defence.
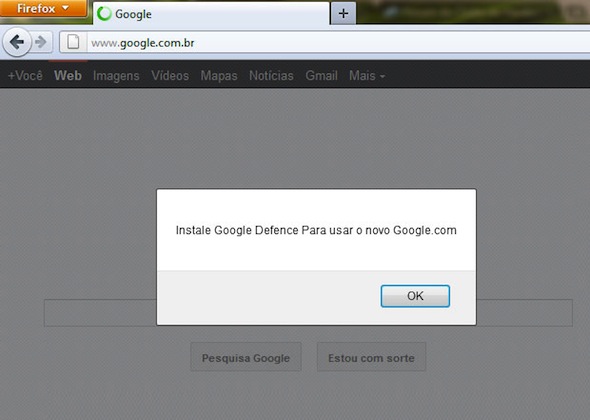
A display encountered by a Kaspersky researcher reads: "To access the new Google.com, you need to install Google Defence"
DNS cache poisoning is frequently carried out by exploiting long-standing security vulnerabilities in the DNS, but at least some of the recent attacks in Brazil appear to be the result of a rogue insider at one of the targeted ISPs.
According to Assolini, a 27-year-old employee of a medium-sized provider in the south of the country has been arrested and accused of participating in the malicious scheme. The researcher provided no other details, except to say that over a 10-month period the unnamed employee had changed the DNS cache of the ISP, redirecting all users to phishing websites.
Assolini also said companies are reporting attacks that are changing the DNS configurations of their routers and modems. As a result, when employees try to visit websites, they encounter displays that instruct them to install a malicious Java applet.
"As described by my colleague Marta in this analysis, several routers and modems have security flaws that enable an external attacker to access and change the configuration of the device,” Assolini wrote. “They are able to exploit security failures and vulnerable configurations such as default passwords.”
In many cases, the malware being pushed on victims is a trojan that steals online banking credentials. ®
