This article is more than 1 year old
Facebook summarily denies undeniable user-menacing security hole
'It doesn't exist...bitch'
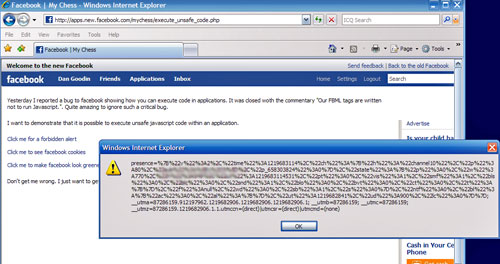
Exclusive Facebook's hip new application platform contains a gaping hole that allows attackers to run malicious javascript on unsuspecting users' machines, a developer has demonstrated.
Proof of concept code examined by El Reg shows how the platform can be used to steal Facebook user's session identification cookies, deliver pop-up messages or change the layout of Facebook pages. With a little extra work, an attacker could probably do much more, including send and read messages from a user's account, change privacy settings and add or delete Facebook friends.
"This is quite a big security hole," said Artur Wachelka, a Munich-based developer of online games who stumbled upon the bug while writing a chess game for Facebook. He said he decided to take the vulnerability public after reporting it to Facebook privately and receiving a single sentence reply that the security issue didn't exist.
Evidently the Facebook drone didn't bother to run the Wachelka's proof-of-concept code. It clearly shows that javascript can be executed on on a browser to display session cookies, display a pop-up windows that says "Oooops" and even change the color of the Facebook banner.
A Facebook spokeswoman said members of the company's security team were investigating the report. As of Monday afternoon, the bug had yet to be squashed.
The bug exists in a component of what's known as FBML, short for Facebook markup language, which developers can use to write games and other applications that run on Facebook. For reasons that aren't clear, a tag that translates text from one language to another fails to parse input for javascript before sending it to users' browsers. The bug appears to work only on Facebook's recently updated pages, and only after users have logged in to their accounts.
All your Facebook session cookies are belong to us
Wachelka said he filed a bug report with Facebook on Friday and promptly received a message saying the matter had been closed. "Our FBML tags are written not to run Javascript," Facebook asserted.
The failure to sanitize the content of third-party applications is one of several privacy and security gaffes that have threatened Facebook users over the past few years. In May they were poked by a cross-site scripting (XSS) flaw, and a separate security hole exposed the private pictures of Paris Hilton and who knows how many other users. Recently, security researchers have reported a worm that attacks users of Facebook and other social networking sites.
Tom Parker, manager of security consulting at Mu Dynamics, a security vendor, examined the proof of concept and validated Wachelka's claim that the vulnerability allowed the execution of arbitrary javascript.
Says Parker: "It's certainly a flaw that needs to be fixed." ®
