Original URL: https://www.theregister.com/2011/08/11/p25_vulnerable/
$25 toy radio used to knock out feds
Thousand dollar radio can track them too
Posted in Legal, 11th August 2011 11:22 GMT
Researchers looking at the security of the US Project 25 radio network, used by federal agents and local police, have discovered that it's easily jammed, and almost as easily compromised.
During a two-year study, the researchers from the University of Pennsylvania found that encryption on the police network was routinely switched off, but also demonstrated how a $25 toy could be reprogrammed to knock out radio transmissions – even being able to exclude specific users or subnets – and how a more-expensive option could track a specific user.
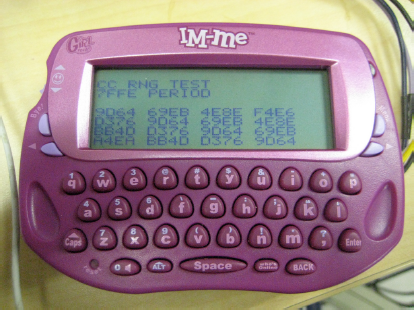
The GirlTECH IMme: Giving girls access to technology was always going to be dangerous
Project 25 is the US equivalent to TETRA, a standard radio platform for local and federal police to communicate in groups during operations. But unlike TETRA, which is deployed in green-field radio spectrum, P25 had to be compatible with the existing analogue systems and is thus squeezed into a fixed 12.5kHz channel, though that's not the only thing making it vulnerable.
The digital system uses fixed-length packets, optionally encrypted using a symmetric key (distributed to handsets manually or over the air). The first problem is that key distribution doesn't always work, so the team found users frequently get cut out and have to ask the rest of the group to switch off encryption for the duration of the operation. Individual users can also, inadvertently, switch off their own encryption without other users being alert enough to notice.
But even when encryption is being used properly, the packet header is sent in the clear, allowing a well-timed jammer to knock out the encryption keys (thus forcing a team to switch off encryption), or knock out transmissions from a specific user. Worse still, a corrupted message addressed to a user prompts their radio to respond with a resent request, allowing an attacker to triangulate the attacked user's location.
The ease with which the radios can be knocked out is alarming, though the researchers did have to spend some months (two years in total) monitoring sections of the 2000 frequencies available to the police to identify bands where interesting conversations were taking place. Having done that, they were able to hear names and locations of criminals under investigation, details of surveillance operations, and plans for forthcoming arrests.
Fortunately, and despite media portrayals, few criminal organisations are quite organised enough to create such an information brokerage.
The researchers' paper (16-page PDF/9.2MB, nicely written but complicated) does have practical advice for users of P25 – reprogramming handsets to make switching off encryption less obvious, and reminding users when it has been switched off – but they conclude that fundamentally the P25 system wasn't designed with a properly layered security model, and that this will always leave it more vulnerable than it should be. ®