This article is more than 1 year old
Hijack wireless mice, keyboards, with $15 of kit and 15 lines of code
MouseJack attack lets you send anything into wireless peripherals radio dongles
Fake wireless computer mice and keyboards can be used to compromise laptops from up to 100 metres away using the portable peripherals from at least seven big vendors including Logitech, Microsoft, and Amazon, software engineer Marc Newlin says.
The attacks target the typically cleartext and insecure communications between a non-Bluetooth port and mouse, as opposed to the wireless link to a keyboard which is often encrypted.
Newlin, of security outfit Bastille, found the attack works against 13 mice and keyboards and reported the vulnerabilities to respective vendors, some of which have posted patches.
Users of unpatched devices are now exposed to some risk of attack should attackers deploy the exploit code and tricks uploaded to GitHub.
Those who cannot update their devices have only the option of throwing out the hardware, although it should be noted that criminals would need to be sufficiently motivated to travel to the physical location of a victim in order to target them.
Newlin says the mousejack attack - which has it's own logo and website - represents a class of encryption-free vulnerabilities that can be exploited with less than US$15 of hardware.
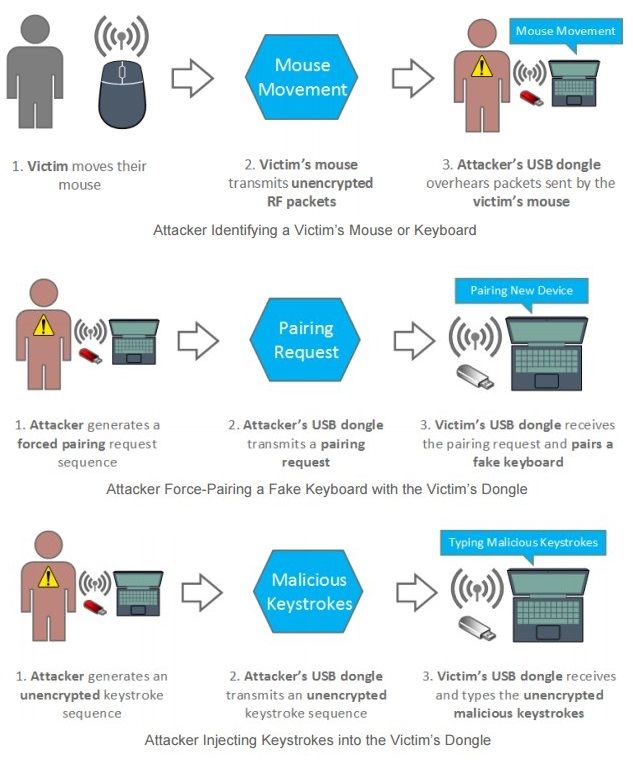
The bad news is that "... there is no authentication mechanism, and the dongle is unable to distinguish between packets transmitted by a mouse, and those transmitted by an attacker," Newlin says.
"As a result, an attacker is able to pretend to be a mouse and transmit their own movement or click packets to a dongle.
"Problems in the way the dongles process received packets make it possible for an attacker to transmit specially crafted packets which generate keypresses instead of mouse movement/clicks."
Nordic Semiconductor is responsible for the nRF24L transceiver series that is used by the bedevilled devices. Newlin recognised this and built a spoofed mouse using an existing homebrew project that housed the nRF24L transceiver within an old-school Nintendo game controller.
Here's how it all came together:
"The nRF24L chips do not officially support packet sniffing, but Travis Goodspeed documented[1] a pseudo-promiscuous mode in 2011 which makes it possible to sniff a subset of packets being transmitted by other devices. This enables the NES controller to passively identify wireless mice and keyboards without the need for an SDR.The NES controller proved to be an excellent platform for learning about the behavior of mouse communication protocols. As opposed to passively collecting data, the NES controller translates d-pad arrows into mouse movement packets, and A/B buttons into left and right clicks. In order to achieve a smooth user experience, it was necessary to create a model of the packet timing and specific behavior expected by the dongle."
A second tool was built with a few lines of Python code for packet sniffing and injection woven into an amplified USB CrazyRadio dongle which included fuzzing capabilities.
Newlin says the vulnerabilities include keystroke injection, mouse and keyboard spoofing, and forced pairing.
Lenovo was also affected by a denial of service vulnerability against its N700 and Ultraslim mouse and keyboards. ®