This article is more than 1 year old
Kiwi hackers crack crap algo, showcase 40c-a-litre DIY fuel discounts
Half price petrol? There's an app for that.
Kiwicon New Zealanders could print their own non-expiring 40c fuel discount vouchers thanks to a shoddy algorithm that a hacking duo has broken.
The algorithm developed by Countdown affects petrol stations operated by national energy provider Z and is designed as an incentive for consumers who shop at various supermarkets.
Countdown says it has developed a "technical solution" for barcode reuse, but it is unknown - and appears unlikely - if this shutters the flaw which allows new codes to be generated at will.
The petrol station had earlier disabled manual barcode entry at pumps to stop codes being shared online, but the researchers say fixing the flaw will require the algorithm to be re-written.
The two researchers, who requested anonymity, have generated the discount codes on a host of different platforms including an unpublished Android app, a barcode printer, and even on tee-shirts.
In a demonstration at the Kiwicon security conference last month the pair demonstrated how with the click of a button their smart watch application would produce codes that could be scanned at the pump for discounts up to 40 cents a litre.
They showcased a barcode printer spitting out valid discounts and finished the showmanship demonstration by scanning a tee-shirt printed with the manipulated code.
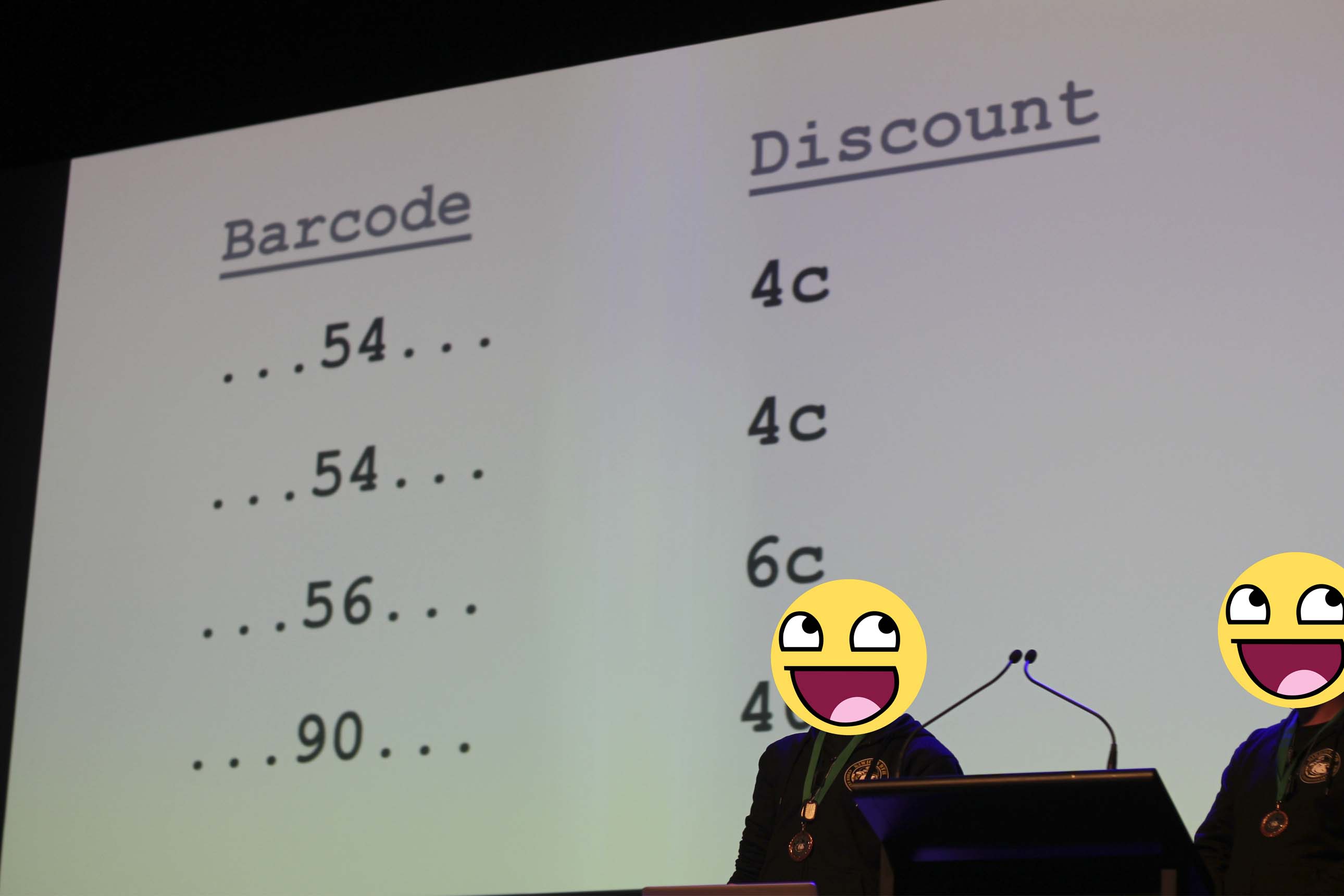
The pair projected the barcode scheme on the huge screen inside Wellington's St James Theatre, directing applauding delegates to spot the blatant weaknesses.
"So you're staring at these codes in Excel and you start to notice a bit of a pattern," one says. "You can kind of see what's happening here - there isn't any kind of crypto."
"All they are doing is x minus 50 equals discount.
They are totally unprotected - there is nothing unique about any part of it."
Multiple security delegates told this reporter they had known and exploited the discount scheme prior to the December 2015 demonstration.
The duo says they have not used the codes on pumps, and urged others to do similar since it would likely be regarded as theft, but say it is identical to the legitimate barcodes offered at retail shops.
Manipulating the algorithm further such that the output is negative could result in a denial of service attack against the petrol pump computers.
Petrol retailer Z told the pair it would keep accepting discount codes for the "majority of customers who aren't stealing from us" noting it can turn off the feature at individual sites.
Countdown told the pair it would eventually shift to unique codes.

A piece of sticky tape is enough to alter the code so T-shirt codes can be successfully re-used.
The researchers told Vulture South fault lies with the design of the algorithm and not with Z. They worked with Z ahead of the talk notifying them of the weaknesses.
Countdown said petrol station operators can detect "unusual activity" through "routine monitoring of self service pumps". ®