This article is more than 1 year old
Been hacked? Now to decide if you chase the WHO or the HOW
Marketers want the bad guys named. Security pros aren't sure they're right
Analysis Imagine a security researcher has plucked your customer invoice database from a command and control server. You're nervous and angry. Your boss will soon be something worse and will probably want you to explain who pulled off the heist, and how.
But only one of these questions, the how, is worth your precious resources; security experts say the who is an emotional distraction.
That's my takeaway after exploring the cyber crime attribution debate for several months, and although it's not the industry's unanimous position: defence intelligence officials, top security thinkers, serving CISOs, ex-cops, and former bank boffins speaking don't entirely agree on on the value of pinning a hack on an individual or group.
A case in point: top security boffins from security firm FireEye -- which carves a name for itself identifying malware groups -- offered polarised opinions on the worth of attribution in two articles posted within 10 days on the very same news site.
That difference of opinion between two senior security people in one of the world's top infosec firms shows that while identifying actors is simultaneously a difficult and expensive diversion of resources, it can also identify how attacks were executed.
On the internet no-one knows you're a dog
Threat intelligence marketers and executives are two forces driving the need for actor attribution. The former is riding something of an industry boom and has irked William Peteroy, owner of startup ICEBRG, and a former security incident responder at Microsoft and technical director of the US Department of Defence's offensive hacker red team.
He and Microsoft mate Paul McKitrick detailed at the Kiwicon conference in Wellington last year what they see as the snake oil elements of threat intelligence, including unnecessary bolt-ons, feeds, and emphasis on actor attribution.
"Attribution has largely become an exercise in scaring potential customers with marketing fear uncertainty and doubt," Peteroy says. "Our main goal in that part of the talk was to call out a lot of the FUD around threat intelligence marketing; specifically we feel like it places emphasis on attribution and quantity rather than actionable components like context and confidence."
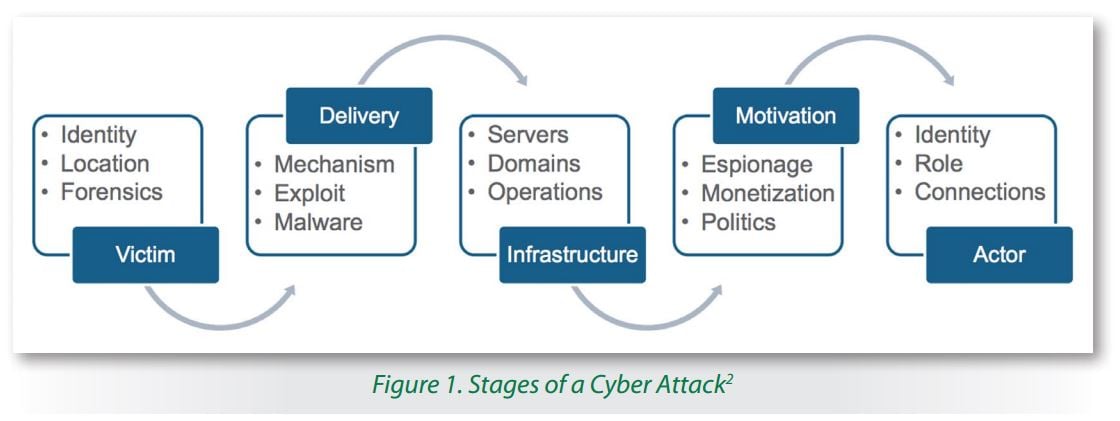
Source: SANS whitepaper [PDF]
The route to successful attribution passes through attackers' Techniques, Tactics, and Procedures (TTPs) which help characterise an attack group and play an critical role in forensic investigations. The acronym has its heritage on the physical battlefield but has become a mantra within the security community as the means by which investigators can identify how attackers break into into networks, and based on those hallmarks to which group they may belong.

Marcus Ranum.
Peteroy says the TTPs are helpful because the data is "actionable" in that it can help direct spending on security defences. "Taking action to mitigate an attack on an organisation or its customers does not necessitate knowing who the attacker is, or where they are from," he says.
Moreover the ability for attackers to mask their actions can make those pursuing actor attribution to look like the Keystone Kops. A public illustration of the folly of attribution is found in the furious attempts to identify, or dox, bragging black hat crews like LulzSec or cyber crime kingpins like former Silk Road boss Ross Ulbricht.
There were literally hundreds of attempts at naming the hacker and the kingpin, and virtually all were wrong. Innocent people were incorrectly listed as members of the hacking teams, and when hunters got it right, and they did, the signal was for a long time lost among the noise.
Yet there is something primal about putting a face to a crime. Stories are unsatisfying when the reader never learns the identity of the killer, and similarly news reports are much more read when the criminal behind the hacking is identified.
This seems to have permeated organisations with executives wanting to know who hackers are. Forensics bods who have worked with major organisations say C-levels will kick up a storm with no regard for the complexities of operational security in their demands to get an identity. A dozen consultants have told this reporter that these requests are common even if the identity of the hacker is not important because the hack was so easy, the network so vulnerable, that any script kiddie could have pulled it off.

Alex Holden.
"I tend to agree that attribution is not only hard but often unnecessary, though I'd phrase it as 'it's so hard it's usually not worth the bother'," says Marcus Ranum, Tenable Network Security senior strategist. "The only part about an attack that you really need to understand is the how and what, not the why and who."
Ranum is a popular thinker in security circles and a veteran of the industry known for his pragmatic, pull-no-punches approaches. He says attribution makes sense only if organisations can respond in a way that will deter future attacks.
Identifying hackers can be a distraction but the process of following breadcrumbs can show the investigator the TPPS by which attackers breach networks. The key is knowing how far to follow the breadcrumbs to uncover the important stuff. "You want to follow the trail far enough to figure out how hackers are penetrating networks," Ranum says. "After that, yeah, it doesn't matter which particular mouse did it - you fix the hole and put your food in metal cans."
Tenable colleague Jack Daniel says as much; "I feel that it is a distraction to most organisations", he says. "It makes for good stories, but not for good security." He says the focus on selling attribution within threat intelligence services dilutes its value, and that it should instead focus on things that help prevent, detect, and remediate threats, and the class of threat actor. "Beyond that, it's not so useful to the vast majority of organisations".
