This article is more than 1 year old
Login creds for US agencies found scrawled on the web's toilet walls
Poor security practices and lack of 2FA responsible for leakiness, says report
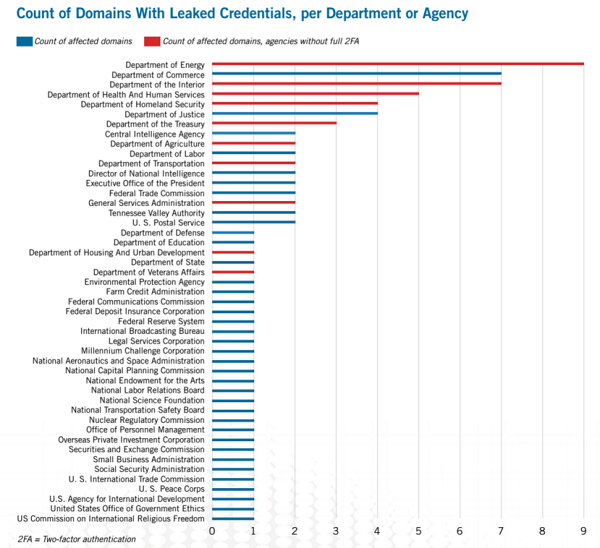
A threat intelligence report into the availability of login credentials for US government agencies has identified 47 agencies across 89 unique domains may be compromised.
The findings resulted from an analysis of open source intelligence (OSint) from 17 paste sites, carried out between 4 November 2013 and 4 November 2014.
The report comes after the February 2015 Office of Management and Budget (OMB) report [PDF] to Congress, which highlighted 12 agencies which did not require their most privileged users to log in with any form of two-factor authentication.
All 12 of these agencies, (including the Departments of State and Energy) had possibly valid login credentials available on the open web, according to the new report by Recorded Future, a web intelligence company.
The credentials must be qualified as being only "possible", as it would have been illegal for Recorded Future to attempt to authenticate them, CTO Staffan Truvé told The Register, but featured domains paired with either plaintext or hashed passwords. Among the domains discovered to have been affected was one belonging to the Office of Personnel Management (OPM).
Citing the recent data breach at OPM, the report notes specifically how a lack of security may leave these agencies "vulnerable to espionage, socially engineered attacks, and tailored spear-phishing attacks against their workforce".
"While some agencies employ VPNs, two-factor authentication, and other tokens to provide a safety net, many agencies lag behind, as cited by the OMB report to Congress," the report claims.
The report also states that while these credentials are often removed, "no efforts are made to contact government agencies whose credentials may be posted on a paste site."
Further, while the information may be removed from a paste site, it likely still circulates in private circles and is available to the original attackers. Due to the lack of context with most publicly announced data exfiltration, it's unclear when specific attacks occurred or if the original attacker had attempted to leverage any stolen information.
Many of the listed government agencies will maintain both classified and unclassified networks: with privileged information stored on the classified networks. However, Recorded Future claims "much can still be gleaned from unclassified systems readily accessible from the open Web, with login portals easily found through simple search engine queries."
The report recommends the following:
- Enable multi-factor authentication and/or VPNs
- Require government employees to use stronger passwords and change with greater regularity
- Gauge and define use of government email addresses on third-party sites
- Maintain awareness of third-party breaches and regularly assess exposure
- Ensure Robot Exclusion Standard (i.e. robots.txt) is set for government login pages to prevent listing of webmail/web services in search engines
In 2010, Recorded Future filed to become a vendor for the NSA, as mentioned in a defensive article on The Intercept. That article was in response to critical coverage of the global surveillance revelations, following Recorded Future's report into How Al-Qaeda Uses Encryption Post-Snowden. The piece made specific note of the company's financial backing from the US security services, via In-Q-Tel. ®
