This article is more than 1 year old
GoGo in-flight WiFi creates man-in-the-middle diddle
Join the mile-high club by getting screwed with fake certs
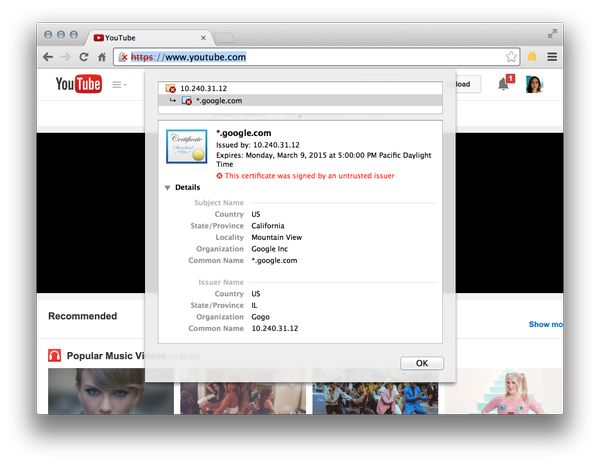
In-flight wifi service GoGo, once accused of facilitating excessive interception access for US law enforcement, has now been spotted using fake Google SSL certificates to spy on net traffic and prevent passengers from accessing video streaming services.
Google engineer Adrienne Porter Felt (@__apf__) noticed the fake SSL certificate which masqueraded as orginating from her employer and publicly called on the company to explain its actions.
Chief technology officer Anand Chari said only that it used the certificates to block streaming services while it upgraded network capacity and did not collect user data.
"Right now, Gogo is working on many ways to bring more bandwidth to an aircraft. Until then, we have stated that we don't support various streaming video sites and utilise several techniques to limit or block video streaming," Chari said in a statement.
"One of the recent off-the-shelf solutions that we use proxies secure video traffic to block it.
"Whatever technique we use to shape bandwidth, it impacts only some secure video streaming sites and does not affect general secure internet traffic."
But there were as Felt said "better ways to do it" other than creating a man-in-the-middle attack against users.
The company's willingness to exceed the mandatory requirements for the provision of telecommunications interception discovered by American Civil Liberties Union technologist Chris Soghoian and detailed by Wired extended the concerns beyond a debate on the legitimate use of bogus SSL certficates.
@__apf__ @gogo @0xabad1dea because they MITM your connection, and pipe absolutely everything to law enforcement. This has been documented.
— Dan Tentler (@Viss) January 4, 2015
In September last year the company revealed in a letter (pdf) submitted to the Federal Communications Commission that it exceeded the requirements of the Communications Assistance for Law Enforcement (CALEA)
Gogo said at the time that an additional capability seemingly the use of CAPTCHA to prevent remote access was an apparent lone function that was not related to traffic monitoring.
The news should serve as a warning to onboard users wishing to keep their data out of government hands. ®