This article is more than 1 year old
Armouring up online: Duncan Campbell's chief techie talks crypto with El Reg
Truecrypt, PGP, GPG - but NEVER Skype
Behind the browser padlock
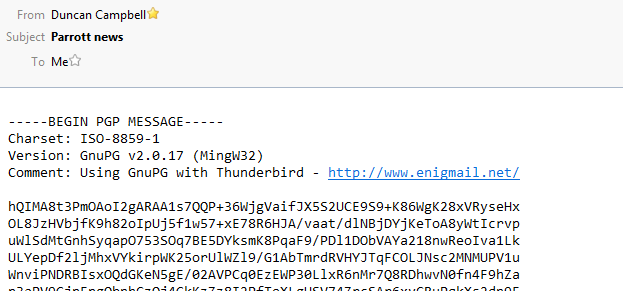
If you've read Glenn Greenwald's recently released book, he describes how the mysterious "Cincinnatus" tried (unsuccessfully) to get him to install and configure GPG, including creating a video tutorial to walk him through the steps; that tutorial is still up and available to view on Vimeo. Although the audio can be a little tricky to understand – he had run his voice through a particularly enthusiastic autotune-like filter to hide his identity – it's a very thorough treatment of how to install and use GPG at a "click here, choose this option" level of detail.
One area that video doesn't cover is how to validate that the Public Key you have found genuinely does belong to the intended recipient. There are known instances of fake keys being uploaded to the public key servers (such as Erinn Clark, developer for the Tor project, and one for Glenn Greenwald himself. This is believed to be how an internal encrypted email between Jesselyn Radack (Edward Snowden's lawyer) and Glenn Greenwald escaped into the wild, as reported here and here.
PGP uses Public Key tools that work with a mathematically-related pair of really massive numbers
In cosy "web browser padlock icon" land, aka SSL/TLS, we all trust a bunch of Certificate Authorities (such as Verisign, Thawte and Digicert). They check the identities of the people they're issuing certificates to – at least, in theory – and the presence of an intact digital signature from the CA means we can be confident that we are genuinely connecting to the site we're trying to reach and not being redirected through an interloper. Of course, those CAs all have to obey the law of the land in their local jurisdictions, National Security Letters and all.
OpenPGP doesn't have that top-down "CA-style" validation of public keys. Rather, users can sign their friends' or colleagues' public keys to assert that they have checked that the specific key really belongs to the proper person. If you verify my key and tell your OpenPGP client that you trust it and trust me, then you will "inherit" the trust I have stamped on to Duncan's key when I signed it. This entire concept, while technically incredibly clever, is also a massive pain in the backside. Accordingly, people don't really do it much or enough – if at all.
The most common approach at the moment is to publish your Public Key directly on your own website. That's a pretty good starting point for most needs, although if you are getting into government-level adversary land then there is still the theoretical risk that either the site has been modified on the webserver or the contents substituted on its way over the internet to you.
To manually verify that the Public Key you're intending to use really does belong to the right person, you need to compare the Key Fingerprint (40 hex digits) that you see on the key with the Fingerprint that the key owner sees on their definitive copy. Counter-intuitively, this process does not need to be done in secret – a Skype or normal-phone call is entirely acceptable. What matters is that the information you're exchanging (fingerprints of public keys) is not changed in transit - there's no specific problem with allowing The Man to eavesdrop on that conversation.
You will see a key ID of the last eight (sometimes 16) digits of a key's fingerprint used to identify it; that is only suitable to use for convenience, it's very possible to forge a key and make the final eight digits of the fingerprint match up with an existing target key. Always validate the entire fingerprint if you're verifying or signing someone's key.
The key-signing side of OpenPGP is pretty un-fun and I haven't managed to find a nice "cuddly" tutorial to suggest at this point. Over to you, commentards?
Skype
Don't even think about using Skype for anything sensitive. There is no meaningful encryption or security provided any more. It is completely open to interception by the agencies. ®
