This article is more than 1 year old
Ruskies use commercial crimeware to mask 'patriotic' Ukraine hacks
BlackEnergy gets a revamp
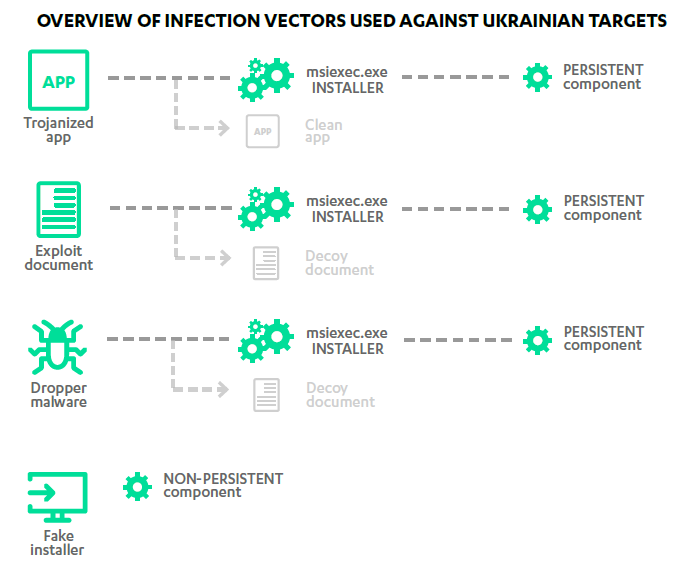
Political hack-attacks are being made to look like bread-and-butter financial fleecing scams, according to researcher F-Secure, after watching Russian hacker collective Quedagh's use of the popular BlackEnergy exploit kit..
The group customised the off-the-shelf malware to attack Ukrainian agencies located in Dnipropetrovsk, in the southeast of the country, the company says, with targets including Ukrainian Rail.
"The use of BlackEnergy for a politically-oriented attack is an intriguing convergence of criminal activity and espionage," researchers wrote in the paper BlackEnergy & Quedagh : The convergence of crimeware and APT attacks [pdf].
"As the kit is being used by multiple groups, it provides a greater measure of plausible deniability than is afforded by a custom-made piece of code."
Quedagh was also implicated in the 2008 denial of service and hacking attacks by Russia against Georgia through suggestive but not conclusive evidence. Its use of financial malware was dated earliest at December 2010, F-Secure said.
ESET researchers separately detected BlackEnergy targeting more than 100 victims spread equally across the Ukraine and Poland.
"We have observed over a hundred individual victims of these campaigns during our monitoring of the botnets," malware analyst Robert Lipovsky said of research presented at the Virus Bulletin conference in Seattle last week.
"[These] include a number of state organisations, various businesses, as well as targets which we were unable to identify."
The updated BlackEnergy kit dubbed version 3 was built over the last four years and included support for proxy servers, user account control bypass techniques, and driver signing features for 64-bit Windows systems (which was added within a month of the Windows 8.1 release).
BlackEnergy was first detailed by Arbor Networks in 2007 as a denial of service bot which in 2010 was upgraded with rootkit technology, support for plugins, remote code execution, and data exfiltration.
The latest incarnation which ESET dubbed BlackEnergy lite had like other malware reduced functionality and sported a lighter footprint as a result.
Quedagh could have been co-opted into carrying out state-sponsored attacks if it wasn't already on Moscow's books, or it was possibly one of many independent patriotic hackers which carried out attacks ranging from very public but simple web defacements to quiet yet advanced bank fraud.
Such groups have existed for decades. Some deface sites with web banners crying for freedom for Palestine or boasting the skills of their nation's hackers, while other well-resourced groups raid state utilities, defence contractors and top end enterprises in what appeared to be state-sponsored attacks. ®
