This article is more than 1 year old
New twist as rogue antivirus enters death throes
That's not the website you're looking for
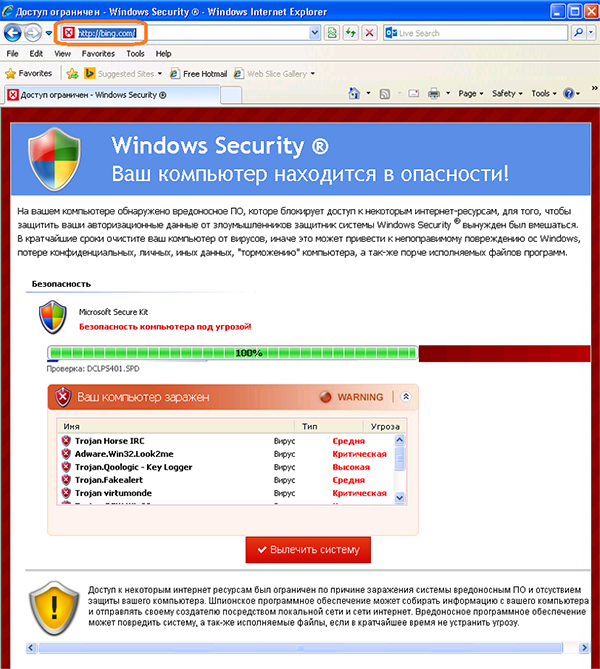
A rogue anti-virus program called Defru has taken to the browser to find a smarter way of infecting users, Microsoft researchers say.
The Defru malware blocks users from visiting certain websites and instead displays warnings about fake perceived threats while the correct intended web address was still displayed.
Most victims are based in Russia, with the US and Kazakhstan trailing behind, Microsoft researcher Daniel Chipiristeanu (@Chipiristeanu) said.
Rogue anti-virus programs have been devastated in recent years by the security industry's fightback. Chipiristeanu showed that infections from the top wares, including Winwebsec, Onescan and FakePAV had plummeted across all global regions since October last year.
Infections were most prolific in the Asia Pacific.
"... since the big malware players are having more trouble in taking advantage of users paying for fake security products, and are moving away from this kind of social engineering, we are seeing other players willing to fill the gap – luckily with small impact," Chipiristeanu said in a Microsoft blog.
"In the past we've regularly seen rogues use the hosts file to block access to a legitimate security product's websites to deny users protection against the threat.
"Defru has a different and simpler approach ... it prevents the user from using the internet by showing a fake scan when using different websites."
He said the proliferation of legitimate, free antivirus products also reduced the likelihood that users would be fooled into download fake AV.
The Defru malware displayed a message on victim machines stating that:
Detected on your computer malicious software that blocks access to certain Internet resources, in order to protect your authentication data from intruders the defender system Windows Security was forced to intervene.
The malware targets 300 websites and uses the hosts file of the victim's machines' to redirect links to a popular fake pcdefender website often used in social engineering.
It promises users to clean their machines and offer updates.
Users can remove the threat with legitimate anti-virus scans. ®