This article is more than 1 year old
Chromecast hack Rickrolls Google's TV stick
Hacker's gonna tell a lie, hacker's gonna p0wn WiFi, hacker's gonna make you cry
Chromecast-owning households may be set to endure Rick Astley's ghastly oeuvre, thanks to a new device that can hijack victims' TV sticks and insert replacement content.
Dan Petro's device, the "Rickmote", is a slick Raspberry Pi box that can knock the Google Chromecast video streaming utility off wireless networks allowing attackers to broadcast custom content on TVs.
Petro writes "... it possible to hijack unsuspecting Chromecast users’ TVs, turning their Game of Thrones marathon into a 1980s flashback ... by briefly disconnecting nearby Chromecasts from their Wi-Fi."
"When this loss of connectivity occurs, the Chromecast tries to reconfigure and accepts commands from anyone within proximity."
Petro warned that the attack was "very rude" because it de-authenticated all visible wireless network. Updates were planned to improve the manners of the Rickmote so that it would take out specific networks.
Google was unlikely to fix the Chromecast flaw because it impacted the core functionality of the device, Petro says. Wired.
The Rickmote Python configuration available on Github was prepackaged with Astley's internet-wrecking hit set to loop.
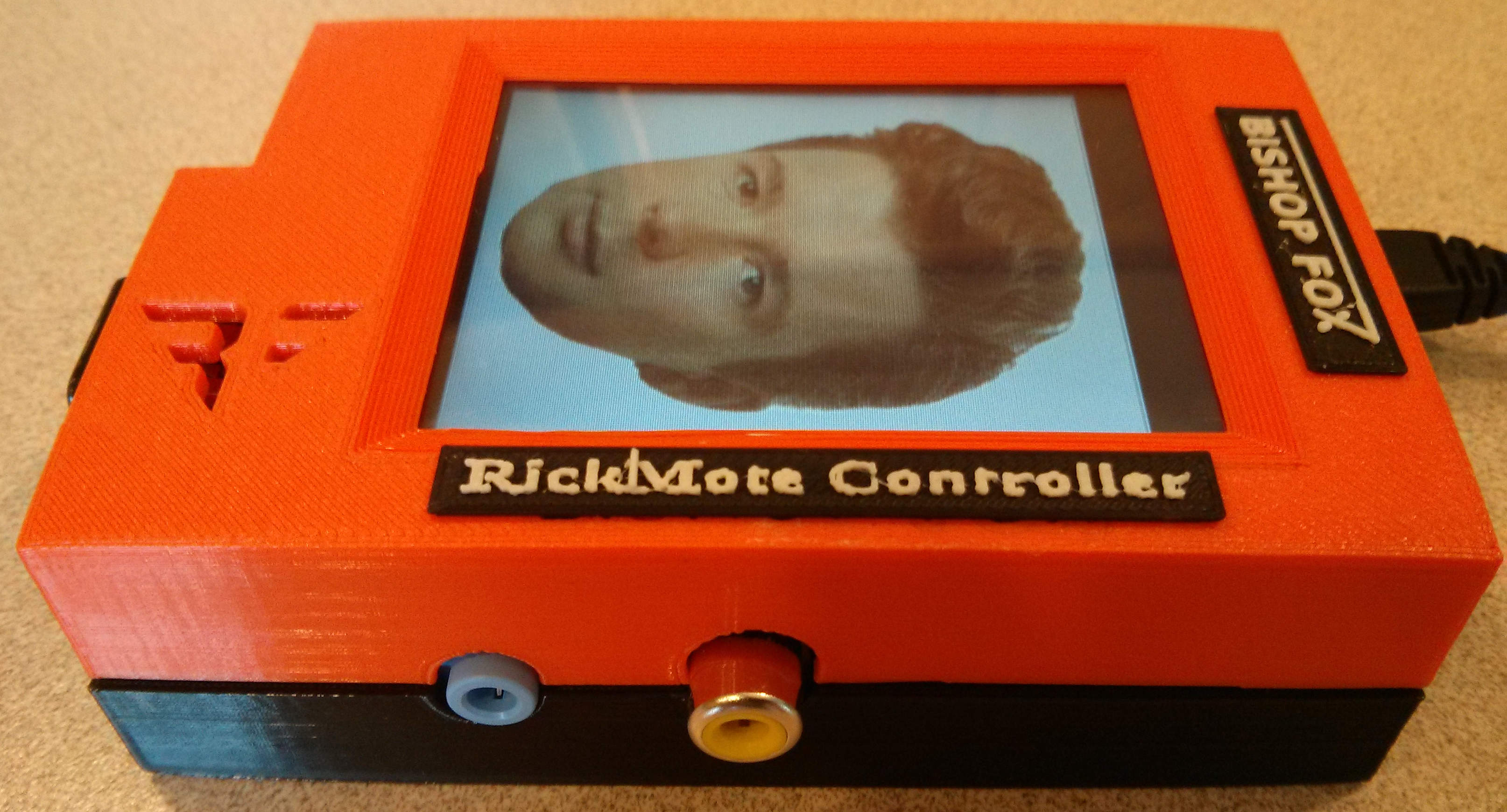
The Rickmote
Attackers needed only to push the "big rickroll button" to raise the blood pressure of any Chromecast users within range.
Full details will be provided during his talk Rickrolling your Neighbors with Google Chromecast at the HOPE X conference in New York tomorrow. Support for attacking Chromecasts with non-Astley YouTube content will be added.
Software dependencies included:
- aircrack-ng;
- Tkinter python library (python-tk in debian);
- hostapd;
- dnsmasq,
- and Network Manager, specifically nmcli.
®
