This article is more than 1 year old
FBI: We found US MILITARY AIRCRAFT INTEL during raid on alleged Chinese hacker
Accused of targeting F-22, F-35 and C-17 planes
A Chinese entrepreneur has been arrested for attempting to steal information on the United States' Lockheed F-22 and F-35 aircraft and Boeing's C-17 cargo plane.
Su Bin – along with two uncharged Chinese co-conspirators – is alleged to have hacked into Boeing's corporate network as well as those of defence contractors in the US and Europe, to gain information the accused said in an email would help China "stand easily on the giant's shoulders".
Su, who had previously operated Chinese aviation firm Lode Technologies, is alleged to have broken into the Boeing network on January 2010, according to a report within a federal complaint unsealed in Los Angeles this week. The suspect and his "co-conspirators" are also alleged to have hacked the systems of other US defence contractors between 2009 and 2013 from a location in China.
The group was alleged to have stolen gigabytes of data on 32 US projects, including what investigators believed was 220MB relating to the F-22.
"Emails between SU and (a co-conspirator) in January 2010 contain at least one lengthy C-17 directory file listing that matches in extensive detail the files and folders hosted on Boeing's computer systems," FBI special agent Noel Neeman wrote.
"These facts show that the C-17 data was ex-filtrated directly from Boeing's computer systems."
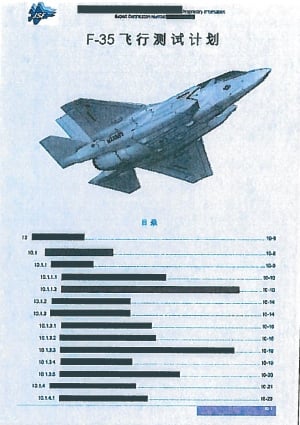
F-35 translated document allegedly stolen and shipped to China.
The report revealed that the co-conspirators' emails saying they'd acquired information on the C-17's landing gear, flight control system and airdrop system – which were confirmed by "experts" to be the first seen by China.
The report claims the two uncharged individuals had boasted of having "repeatedly skipped around" within the internal network to evade detection using a "prodigious quantity of tools, routes and servers".
To Boeing's credit, they apparently said the internal network was harder to crack than they had anticipated and added that they'd used proxies in countries that were not friendly to the US.
They were further said to have targeted executives at an unnamed US firm and another company involved in weapons control and "electronic warfare systems". Intel on commercial airplanes was also apparently targeted.
Su was arrested on 28 June by Canadian mounties at the request of the FBI. The complaint revealed his aviation company maintained an office in Canada and alleged that Su and his "co-conspirators" had swiped large amounts of data relating to "dozens of US military projects" which he allegedly wrote would allow China "to rapidly catch up with US levels."
The China-based co-conspirators were said to have performed "network reconnaissance and intrusion operations" and were said to have received requests to steal key documents identified by Su.
Su was also said to have attempted to sell off intelligence to state-owned companies in China for personal profit.
The report quoted the alleged hacker group as claiming 630,000 digital files relating to the C-17 cargo plane were stolen, amounting to 65GB.
The group was also alleged to have stolen information on a US unmanned aerial vehicle project and the contractors involved including gaining credentials for one company's customer management system.
In emails, the conspirators revealed they have previously targeted Tibetan democracy and independence movements but had shifted crosshairs to military technology.
Su is scheduled to appear in a Vancouver court this month. ®
