This article is more than 1 year old
Weaponised Flash flaw can pinch just about anything from anywhere
This is a 'patch now or regret it sooner-rather-than-later' mess for you and webmasters
Get cracking with the latest Flash upgrade, because the vulnerability it patches is a peach, allowing a cross-site request forgery (CSRF) attack for stealing user credentials.
According to the Switzerland-based Google engineer that turned up the vulnerability, Michele Spagnuolo, sites that are/were vulnerable to the attack included various Google domains, YouTube, Twitter, Instagram, Tumblr and eBay.
“I present Rosetta Flash, a tool for converting any SWF file to one composed of only alphanumeric characters in order to abuse JSONP endpoints, making a victim perform arbitrary requests to the domain with the vulnerable endpoint and exfiltrate potentially sensitive data, not limited to JSONP responses, to an attacker-controlled site,” Spagnuolo writes.
Rosetta Flash takes a combination of three characteristics of Flash and JSONP which he says were all “well known” but ignored, since nobody had previously worked out how to combine them into an attack.
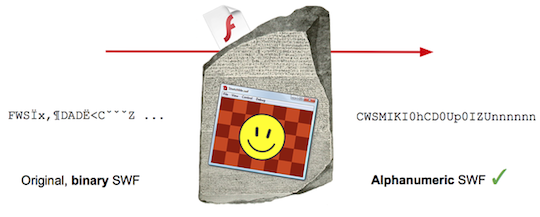
Rosetta Flash creates alphanumeric-only SWFs that can be used to embed a JSONP CSRF attack.
Image: Michale Spagnuolo
The first component of the attack is that a SWF file can perform cookie-carrying GET and POST requests to the domain that hosts it, with no cross-domain checks. As a result, Spagnuolo writes, a site that lets attackers upload SWF files on a sensitive domain “can make the victim perform requests that have side effects and exfiltrate sensitive data to an external, attacker-controlled, domain”.
The second part of the attack uses JSONP: this, he writes, “allows an attacker to control the first bytes of the output of an endpoint by specifying the callback parameter in the request URL”. JSONP is usually restricted to alphabetic characters only – and this is where Spagnuolo's Rosetta Flash tool turns the SWF/JSONP combo into an attack.
The third part is that an SWF file (with a content type-forcing
