This article is more than 1 year old
Facebook scuttles 250k-strong crypto-currency botnet
As noose tightens, VXer pleades: 'Stop breaking my ballz'
Facebook has taken down a Greek botnet that at its peak compromised 50,000 accounts and infected 250,000 computers to mine crypto-currencies, steal email and banking details and pump out spam.
The scuttled Lecpetex botnet spread malware including the DarkComet remote access trojan by social engineering techniques and was adept at avoiding anti-virus and detection by white hat researchers.
Security boffins at Menlo Park said the 31 and 27 year-old botnet authors delivered 20 distinct spam campaigns between December and June this year before they were arrested last week.
"On April 30, 2014, we escalated the Lecpetex case to the Cybercrime Subdivision of the Greek Police, and the agency immediately showed strong interest in the case," Facebook engineers wrote in an unauthored post.
"According to the Greek Police, the authors were in the process of establishing a Bitcoin 'mixing' service to help launder stolen Bitcoins at the time of their arrest.
"Ultimately, remediating a threat like Lecpetex requires a combination of technical analysis capabilities, industry collaboration, agility in deploying new countermeasures, and law enforcement cooperation."
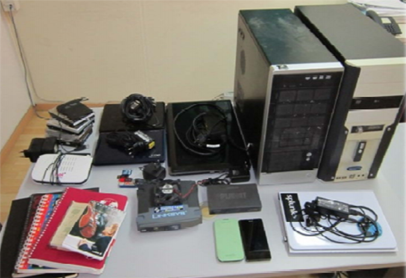
Botnet bits. Source: Greek Police
It was the 'most important' case the Greek Cyber Crime Unit has handled, according to local paper the GreekReporter, (which we fed into transaltion engines). The malware was said to have pinched an email password tied to the Greek Ministry of Mercantile Marine.
Police found scores of hijacked passwords and 114 hijacked crypto currency wallets in the raid. They seized four laptops and USB sticks, nine hard drives and two desktops, according to a police presentation [pdf, Greek].
Lecpetex was a smattering of Windows modules that swiped Facebook account credentials to further distribute itself through private messages. Modules could download counter anti-virus updates and arbitrary executables including DarkComet and variations of the Litecoin mining kit.
It also spread through malicious torrents but this was not observed by Facebook bods.
After five months of probing, irritated vxers began leaving messages for Facebook folk in their command and control servers.
"[They] started leaving notes for our team such as 'Hello people.. :) <!-- Designed by the SkyNet Team --> but am not the f***ing Zeus bot/Skynet bot or whatever piece of sh*t.. no fraud here.. only a bit of mining. Stop breaking my ballz.."
They also changed their crypto keys to the phrase 'IdontLikeLecpetexName'.
Lecpetex malware used a Java JAR executable or a Visual Basic Script to fetch the main module loader from a variety of URL-obfuscated cyberlockers. The local Java installation meant sandbox restrictions did not apply allowing the JAR to read and write local files as well as execute arbitrary commands without using an exploit.
Facebook has previously taken down botnets including Mariposa and the Koobface worm.
Menlo Park used its inhouse ThreatData tool to help crack-down on the botnet. That tool blended long and short -term intel to improve incident response. ®
