This article is more than 1 year old
Google's URL-hiding 'origin chip' is 'backburnered'
Translation: insecure feature scammers would have loved has been binned
Google has “backburnered” a controversial feature that would have hidden full details of web addresses from Chrome users.
The feature was called “origin chip” and, as we explained a few weeks back it removed all the characters beyond the top-level-domain from Chrome's Omnibox, as you can see below.
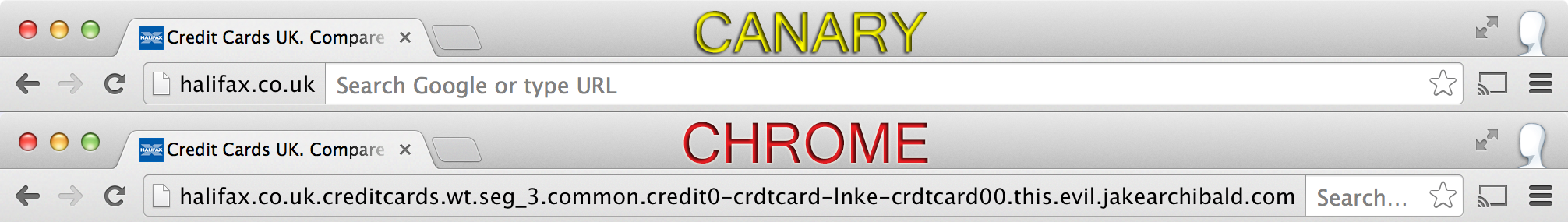
The ad-slinger's rationale for origin chip was to tidy up the browser and highlight the sites users visit, to foil attacks that rely on spoofing sites with subtle variations on real sites' names. In one case the address halifax.co.uk was replaced with a long subdomain address punctuated with many full stops that pointed to a phishing site. If that site's actual address was front and centre, Google suggested, the phish would not have worked.
Critics pointed out that all sorts of criminals love the idea of users seeing only a domain name because if Joe or Jane Average sees www.google.com they're not going to be able to see the likes of www.google.com/this_page_is_malware_planted_by_a_phisher.
Whatever the merits of either argument, this thread on the Chromium developers' forum suggests “the origin chip work is backburnered”.
Let's assume that means it's not under active development for imminent versions of Chrome, shall we? And add crimes against grammar to our list of gripes to direct towards Google. ®
