This article is more than 1 year old
Bitcoin ransomware racket makes bank
Thousands paid, but Durham says it won't be bowed
Criminals appear to be pocketing hundreds of thousands of dollars with upgraded Cryptowall ransomware that has encrypted scores of hard drives across Britain, America and Australia demanding victims pay hefty Bitcoin ransoms.
The ransomware was foisted on victims through sneaky malvertising through unsuspecting big ticket sites including Facebook, The Guardian and eBay.
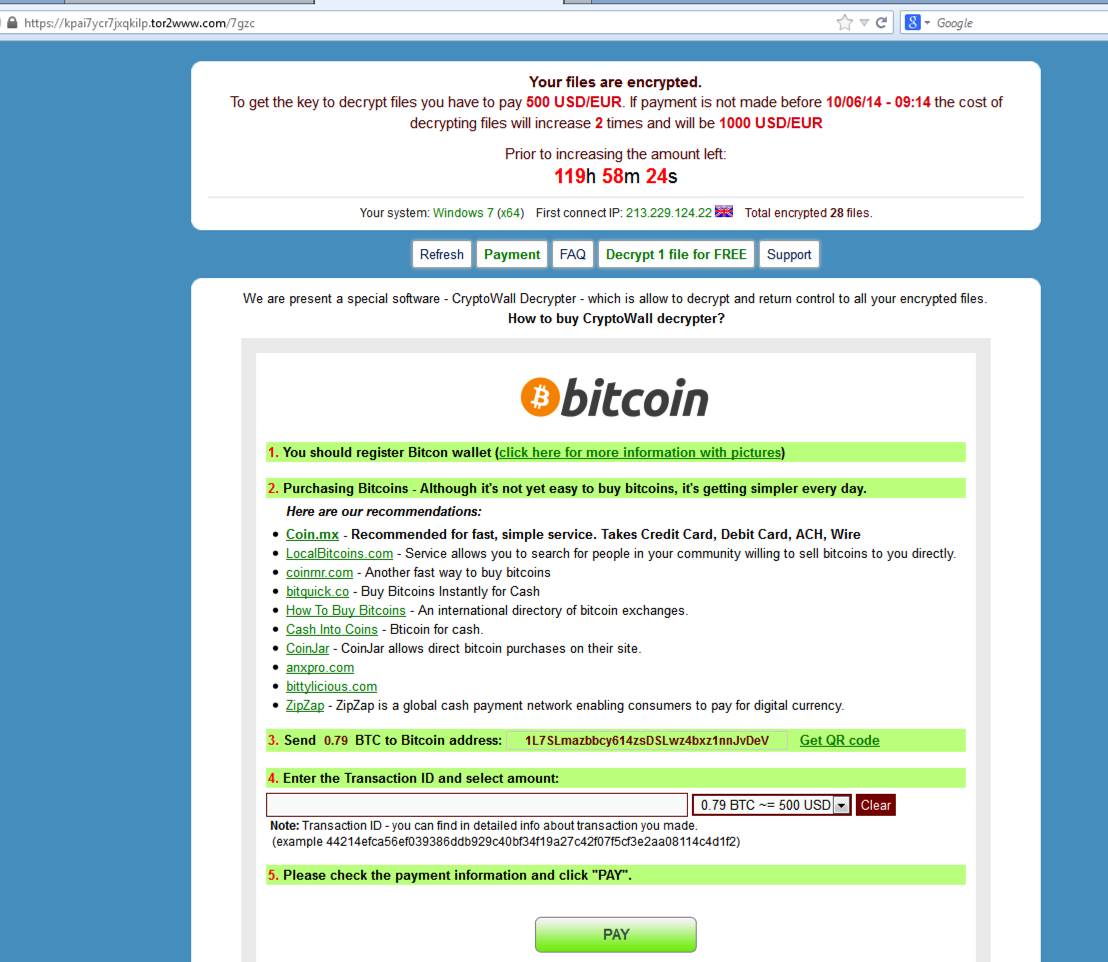
Cryptowall locked down victim files on local and attached storage devices with RSA-2048 encryption implemented well enough that no public side channel attacks have yet been reported.
Victims were asked to pay $US500 to unlock encrypted drives within a short period for face exponential increases in ransom.
Bitcoin blockchains linked to only a handful of scams reported to PhishMe and found by El Reg scattered across the internet show by way of blockchains that hundreds of Bitcoins have been deposited into the crims' wallets, equating to more than $100,000.
The success of the scam since Cryptowall was bundled into the popular RIG exploit kit indicates that criminals have made huge profits from the crime.
But the tenacious town of Durham has thumbed its nose at the scammers with police proclaiming they would rather deal with the fallout of encrypted computers than pay the unscrupulous crooks.
"Make no mistake, the Town of Durham will be paying no ransom," town manager Todd Selig (@tselig) said.
Police were able to restore machines from backup while staff returned to pen and paper.
Others have been far less fortunate. PhishMe reported one of its Greek users had lost up to 32,000 files to the ransomware and another in Canada had 21,000 encrypted.
Senior researcher Ronnie Tokazowski (@iHeartMalware) estimated some 348,610 victims were potentially infected by examining the base 36 number scheme used to generate unique TOR payment pages for victims.
The malware had been revamped since the earlier CryptoDefence incarnation was found to contain the decryption key within its codebase.
Cisco warned the new version was booming and had blocked 90 domains linked to Cryptowall and the RIG kit that targeted 17 percent of its cloud web security customers.
Users of unpatched versions of Flash, Java and Silverlight were open to attack.
El Reg strongly recommends users maintain air-gapped backups of critical data as synchronised cloud backups which could also be affected. ®