This article is more than 1 year old
How Bitcoin could become a super-sized Wayback Machine
Why mine maths when you can ARCHIVE STORAGE!
Researchers have proposed a system which could see Bitcoin users earning their trendy tender by replicating vital data sources rather than crunching pointless algorithms.
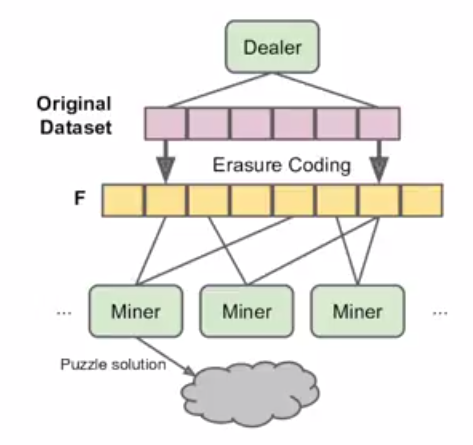
The new system, dubbed Permacoin by a team of University of Maryland and Microsoft researchers, would substitute the current requirement to obtain Bitcoins through crunching mathematical algorithms with a system where punters replicated important datasets.
It would function as a "free" guard against wholesale data losses from cloud providers, and could see valuable sources such as the 200Tb US Library of Congress backed-up if it were applied to the current Bitcoin network, researchers wrote in a paper (pdf).
In the case of the recent US Government shutdown in which agencies were shuttered for two weeks, the network would have ensured the Library of Congress was accessible.
PhD Andrew Miller said this would bolt-on a "massively diverse global replicated storage system" to crypto-currency mining.
"[It is] a variation of Bitcoin where instead of miners using SHA2 they will instead be using storage equipment that would be storing important data sets," Miller said.
"Users could add their own data to archive [which] could be recovered in the event of catastrophic failure."
Data replicated from sources would need to be validated through a series of checks, or Proof of Reliability. These checks would take about six seconds to validate a day's work of replicating the US Library of Congress, Miller said.
If the Bitcoin network used the storage model instead of processing algorithms, the researchers estimate 120 terabytes could be stored if users contributed 4 GB and could stretch to 100 petabytes if users spent on solid state storage rather than the popular Avalon ASIC mining hardware.
Users could begin mining with small USB sticks and basic processing capacity. The storage would need to be saved locally and not in cloud services such as Amazon which would reduce the diversity of stored data and weaken disaster recovery.
Punters would be prevented from storing data in cloud services by the use of a secret key (floating preimage signature) required for mining and to move a users' currency.
This could wipe out the current array of mining pools common in Bitcoin where users link compute power to earn the increasingly rare coins.
Users could also nominate the data they would like to replicate but could not select random information which may benefit attackers or be chosen for ease of processing.
Researchers have built a Permacoin prototype and will continue to develop the system. ®