This article is more than 1 year old
Police at the door? Hit the PANIC button to erase your RAM
App wipes memory, encrypts hysterical hacker boxes
The next time the police kick down a hackers' door, suspects can reach for the Panic button to make it nigh-on impossible for plod to recover any data, even if they freeze their target PCs.
The Panic button is a new Python app called "Centry Panic" and was developed to mitigate cold boot and direct memory access attacks on Windows, Mac and Linux that could be used by forensics professionals to capture information from memory.
Cold boot attacks allow the fading contents of RAM to be preserved for reading after a target machine is shut down. Direct memory access side-channel attacks allow crypto keys to be yanked by attackers with access to the physical memory address space of a target machine.
Both attacks work after a computer's chips are chilled by about ten degrees centigrade, as doing so noticeably delays memory fade on systems running DDR1 and DDR2, according to a paper (pdf) published last year on the feasibility of cold boot attacks.
However the short window of time available to pull meaningful data in cold boot attacks coupled with the techniques failure to target DDR3 RAM raised doubts that the attacks were feasible. Academics said the lower voltage, higher integration density and resulting lower charges in DDR3 ram cells could explain the failure.
One experienced Melbourne forensics bod told El Reg he had not heard of any Australian Government agencies or police units using the technique, dubbing it a trick limited to the academic realm.
Even if cold boot attacks may not be effective in the real world, Centry Panic means villains and hacktivists have a way to defeat them.
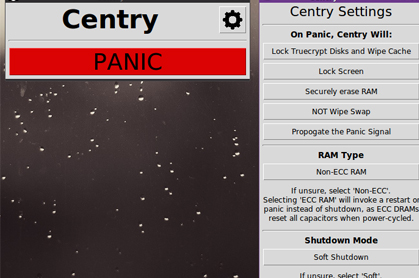
The Python application is replete with a shiny graphical user interface would lock down Truecrypt disks, erase keys and overwrite RAM before shutting down a targeted system.
It can also propagate the panic commands to other nodes on a network.
Centry could be downloaded for free on GitHub. Its cryptographically-inclined developer was reachable on Twitter, where he is known as @0xPoly. ®