This article is more than 1 year old
Privacy International probes GCHQ's mouse fetish
Asks Dell, Apple et al why Grauniad's Snowden-sodden peripherals deserved drilling
Privacy International is probing hardware manufacturers about what data can be stored on peripherals after it was revealed the GCHQ specifically targeted trackpads, keyboards and monitors in its destruction of Snowden files held by the Guardian's UK office.
Blighty's G-Men oversaw the destruction of storage devices and computers that contained encrypted secret NSA documents leaked by former contractor Edward Snowden.
The destruction continued despite Grauniad telling spooks the data was duplicated off-shore prompting suggestions the risible ham-fisting was grounded in paranoia or PR.
The claims may receive more weight after a joint probe by Privacy International and the Guardian found Blighty also ordered the destruction of peripherals which according to conventional thought would not contain Snowden-related data.
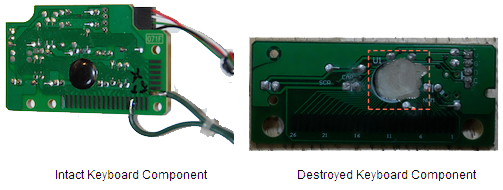
G-Men specifically ordered that keyboard, trackpad and inverting converter chips be destroyed. Their preferred drilling techniques are depicted below.
Privacy International, after prompting from technically-minded folks, has asked Apple; Microsoft; Dell; HP; Logitech and Synaptics about what data can be stored on the chips and for how long.
"During our investigation, we were surprised to learn that a few very specific components on devices, such as the keyboard, trackpad and monitor, were targeted along with apparently trivial chips on the main boards of laptops and desktops," Privacy International's Dr Richard Tynan said in a post.
"By getting answers to these questions, we can get a glimpse into GCHQ's understanding of IT security threats, but also give individuals the information to better understand the devices they use everyday and how they can protect their personal information.
"For instance, people and organisations may need to re-evaluate how they dispose of their computing devices, given the very specific hardware components destroyed by GCHQ."
Tynan hoped vendors would reveal the manufacturers of the destroyed chips and describe the specific role the electronics played in the operation of peripherals.
Government devices containing sensitive data such as the Snowden documents were required to be encrypted to defence security standards (pdf). This prompted one forum user claiming to be a former British intel officer to suggest the chips were regarded as tainted and were destroyed as standard practice.
The privacy warriors quizzed five vendors on the capabilities of a keyboard encoder used in different branded peripherals, and asked Apple about the function of the MacBook Air's trackpad serial flash chip.
Cupertino was also asked about the Air's inverting converter thought to be similar to a model listed online.
Tynan called on the tech industry to help with further investigation into other shredded chips in its bid to shed light on how the components may "betray privacy". ®
