This article is more than 1 year old
Malware-as-a-service picks Android apart
Dev offers crimeware roadmap to subscription customers
Quite possibly the most expensive and capable Android malware the world has yet seen is for sale at $US5000 on underground markets, replete with software-as-a-service support.
The iBanking malware has evolved from a simple SMS-stealer to a highly capable application that records audio within the range of a device's microphone, steals contacts, and records, uploads and redirects phone calls.
iBanking could be a watershed for the mobile platform as it showcases the extent of damage possible by malware.
Blackberry appears next on the hit list for the malware's maintainer, an entity known only as "GFF" announcing a version planned for development.
Most Android malware such as the Zeus (ZITMO) banking trojan were constrained to nabbing credentials and two factor banking tokens, and could be easily removed.
With the latest upgrade made August, iBanking could access the platforms' file system, hide application code, and send SMS and prevent removal of the malware if administrator rights were enabled on the infected device.
GFF sold the expensive app to well-resourced crime gangs that received patches, updates and software support.
The serviced model was increasingly popular with virus and exploit kit writers and had ensured GFF kept paying clients after the iBanking source code was stolen and leaked online in February.
The fallout however was worse for Android users according to Symantec researchers who reported a surge in iBanking activity since the leak.
"Symantec predicts that this upsurge in activity will continue as news of the leaked source code spreads through the underground," researchers wrote in a post.
"However, we believe that the more professional cybercrime groups will continue to pay for the product, allowing them to avail of updates, technical support and new features."
The silver lining was that the leaked and unsupported version in use by criminal pirates contained a unpatched vulnerability which may be later used by white or black hats bring down command and control servers.
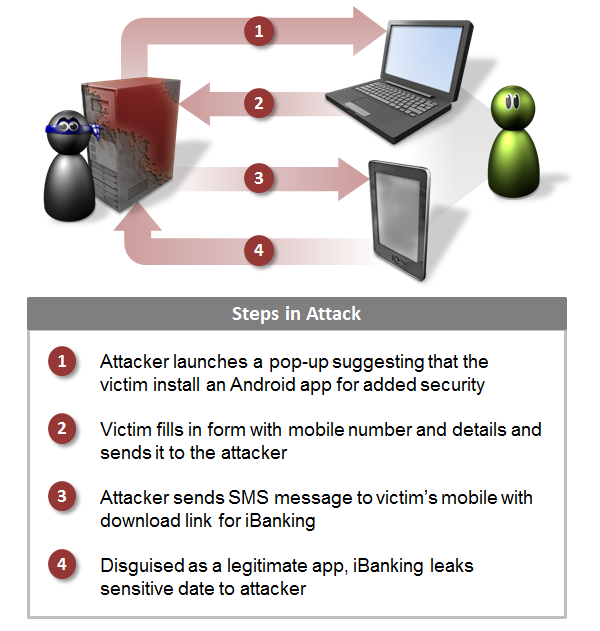
There was further reprieve in that users had to accept a laundry list of permissions for full compromise to occur but that was offset by some clever infection techniques.
Infection happened over social media networks, phishing sites and via pop-up messages generated by Windows trojans. ®
