This article is more than 1 year old
Hacktivists hijack BNP Twitter account, crayon over leader Griffin's too
I'm the leader of the Gay Orgy Party and we just LOVE immigration, guys. Mwah!
Hacktivists from Anonymous took over the Twitter feeds of the extreme British National Party and its controversial chairman Nick Griffin over the weekend.
The hack against @NickGriffinMEP's profile, which boasts 29,000 followers, was apparently mere mischief rather than a desire to make a point against a politician notorious for his views on ethic minorities, homosexuals, immigrants and many others.
Griffin's bio was modified to read that it was the "official twitter page of British Gay Orgy Party Chairman and Member of the European LGBT Community for the North West region, Nick Griffin".

Hacked: The BNP stand against gay marriage.
The attacker claimed in a Twitter update that the BNP used the same password in a number of places, paving the way towards the multiple account hijack.
We only have the word of a hacker calling himself Anon_0x03 for this but it's a more than plausible scenario. Hacktivist types often use password hash dumps from the recent breach of Yahoo! email accounts (and others) to expose weak passwords before trying them against other accounts maintained by the same user elsewhere.
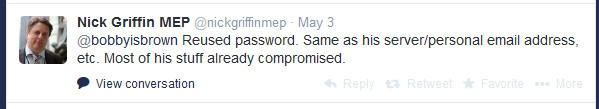
Recycled passwords: Failing to follow basic infosec tips led to the BNP losing control of its Twitter accounts.
The Twitter account of Griffin’s party, the BNP, was also hacked over the weekend.
The @bnp Twitter bio was changed to describe it as a "pro-immigration" party, which is certainly not the case. Neither account has been restored to its "rightful" owner as of Tuesday morning. Both Twitter profiles are linked to through various articles on the official BNP website, which appears to have been unaffected.
The attacks both took place over an extended bank holiday weekend in the UK – and just three weeks before upcoming European Parliament elections.
Veteran security expert Graham Cluley comments on the hacks, which illustrate the dangers of password reuse, in a blog post here.
Four years ago, prior to the last Euro elections, the BNP launched a fund-raising drive after it claimed it was hit by the biggest DDoS attack ever. Independent security experts said the attack failed to register on their systems. ®
