This article is more than 1 year old
Tech giants KNEW about PRISM, web snooping, claims top NSA lawyer
US govt denies it did anything wrong as squabble over semantics continues
Analysis The NSA's general counsel Rajesh De says technology firms were fully aware of both America's web surveillance program PRISM and the mass monitoring of upstream internet traffic.
On Wednesday, De told a meeting in Washington, organized by the US government's Privacy and Civil Liberties Oversight Board (PCLOB), that data collection by secret order under Section 702 of the FISA Amendments Act was carried out with the “full knowledge and assistance of any company from which information is obtained,” The Guardian reported.
Internet giants, particularly Google and Facebook and Yahoo!, have over the past nine months blasted the intelligence agency's methods and denied any collusion. Let's tackle De's statements in two halves.
Looking through the PRISM
To recap, according to documents leaked by the whistleblower Ed Snowden last summer, the PRISM system allowed the NSA to tap up web giants to access users' email, instant-messenger logs, any stored or transferred files, voice chats, photos, videos, and so on.
When the top-secret program was revealed, Apple, Google and others accused of participating in the scheme angrily denied all knowledge of PRISM.
“PRISM was an internal government term that as the result of leaks became the public term,” De told the privacy board in Washington. “Collection under this program was a compulsory legal process, that any recipient company would receive.”
Once again in the Snowden saga, this is a game of semantics: last June, Apple, Google and others claimed they had never heard of the term PRISM; De is saying they did but by another name – because PRISM was just an internal codename until Snowden leaked it to journalists.
All of the corporations involved were, at the time PRISM emerged in public, limited by law in exactly what they could say, however they have since published the number of requests they have received from the US government for netizens' private data.
The rub seems to be this: the Snowden leaks suggested the PRISM surveillance was widespread, in real-time and automated, or nearly so; De claims the internet companies involved knew of the PRISM system and cooperated; and said companies denied they knew anything about it, but later acknowledged they were compelled to service requests from the US government for personal data.
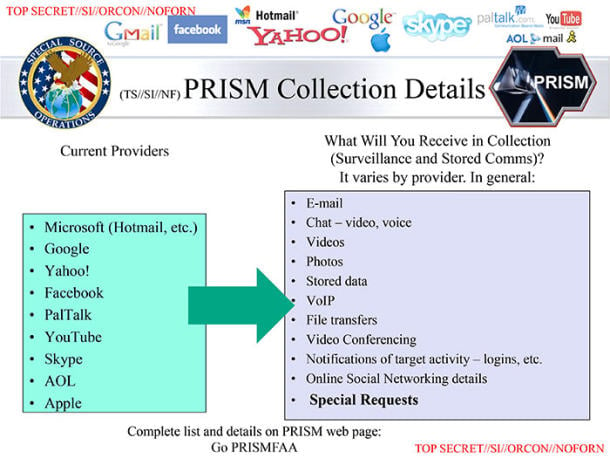
Judge for yourself ... the leaked top-secret slide detailing the information that can apparently be obtained by the NSA's PRISM system (click to enlarge)
Upstream traffic collection
Again according to slides leaked by Snowden to the press, analysts at the NSA and Britain's GCHQ were sifting through upstream traffic in transit through the fiber-optic cables that form the arteries of the global internet. The spies also monitored connections between firms' data centers, particularly Google's and Yahoo!'s.
Google, Facebook and others reacted furiously to revelations that the NSA and GCHQ had intercepted users' web traffic, denying any knowledge of it when such claims were published last year. Telcos, such as Level 3 and BT, that provide the links between data centers and the upstream connectivity had little to say on the subject.
Just to reiterate what was said this week, when De was asked whether data was collected by the NSA with the "full knowledge and assistance of any company from which information is obtained," he replied: "Yes." But it's not clear exactly who De is referring to here, whether it's just the backbone telcos, the websites spied-upon netizens were accessing, or both.
Drilling into the claims – only to find silence
El Reg today contacted all of the companies named as being participants in the PRISM program and requested clarifications in response to De's latest statements. None were willing to go on the record, but a couple of the firms commented under the condition of anonymity.
Both told a similar story: yes, companies that received federally mandated orders to cooperate in secret did do so, but the g-men weren't given direct access to servers. Both firms then insisted they had no idea of the upstream side of the monitoring program, one calling the idea "ridiculous."
At the PCLOB meeting this week, deputy assistant attorney general Brad Wiegmann insisted that the American government and the NSA had acted within the law at all times. Searches of netizens' private data, collected in bulk under the Foreign Intelligence Surveillance Act, were reviewed once a year by a secret court, and Wiegmann said any other system would be impractical.
"If you have to go back to court every time you look at the information in your custody, you can imagine that would be quite burdensome," he said. ®
