This article is more than 1 year old
WhatsApp chats not as secret as you think
Malicious apps can steal chat history
Mark Zuckerberg's $19bn darling, WhatsApp, isn't as secure as we thought: a Dutch researcher has found that chats can be accessed and read by other apps.
Bas Bosschert has described a process by which the chat database can be read even if it's encrypted. His proof-of-concept, here, runs through the process.
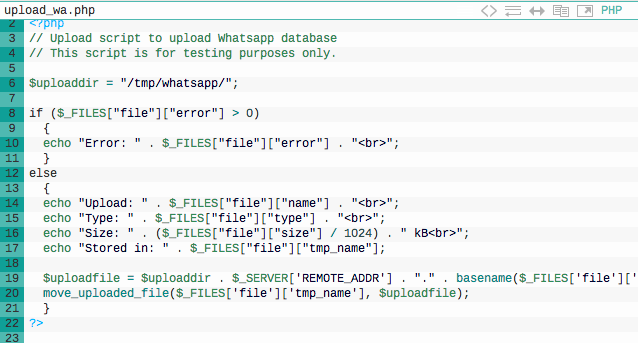
Here's the short version: Bosschert first created a php Web server to run on the target device, then with a bit more code work, he uploaded the WhatsApp message files to his own app – msgstore.db and wa.db for older versions, msgstore.db.crypt for newer versions.
If an attacker was to “combine it with something like FlappyBird and a description how to install applications from unknown sources,” he writes, “you can harvest a lot of databases”.
Bas Bosschert has worked out how to read WhatsApp stored chats
For unencrypted stores, the work's already done. For newer versions of WhatsApp, he writes, decryption is already available from the WhatsApp Xtract backup tool.
For Bosschert's attack to work, all that's required is that the user grants sufficient permissions to the malicious app. As he writes: “ since [the] majority of the people allows everything on their Android device, this is not much of a problem.” ®
