This article is more than 1 year old
NSA's TURBINE robot can pump 'malware into MILLIONS of PCs'
Sysadmins, routers, criminals' IRC botnets, and maybe terrorists, all for the pwning
Updated The latest batch of top-secret intelligence documents from the hoard collected by NSA whistleblower Edward Snowden detail the massive increase in the agency's use of its Tailored Access Operations (TAO) hacking unit – including a system dubbed TURBINE that can spam out millions of pieces of sophisticated malware at a time.
The presentation slides, published by The Intercept, show that 10 years ago the NSA had infiltrated and tapped a modest number of computers, but has since hugely bolstered its toolkit and increased its target list. Within eight years, the number of active pieces of implanted spyware was in the tens of thousands, and slides show an extensive arms catalog of malware for the TAO team to choose from.
"One of the greatest challenges for active SIGINT/attack is scale," explained one presentation from 2009, marked top secret. "Human 'drivers' limit ability for large-scale exploitation (humans tend to operate within their own environment, not taking into account the bigger picture)."
The solution was to build TURBINE, which can carry out "automated implants by groups instead of individually," and scale to operate millions of implants at a time. This command-and-control server includes an "expert system" that automatically picks the right malware for a victim and installs it on their computer, thus "relieve the [TURBINE] user from needing to know/care about the details."
TURBINE was active from at least July 2010, the documents state, and has infected up to 100,000 devices and machines, with more planned. According to the agency's 2013 budget files, some of the $67.6m of taxpayer dollars allocated to the NSA's TAO team went to maintaining and developing the system.
TURMOIL hunts the sysadmin
TURBINE also links into a NSA sensor system dubbed TURMOIL, which taps into computer networks around the world to monitor data traffic and identify potential targets. It can track down a mark from their email address or IP address, which device he or she is using, or by web cookies from Google, Microsoft, Twitter, Yahoo! and others.
While terrorist targets are mentioned, it's clear from the documents that system administrators are also high on the todo list for the TAO team. One comment on an internal NSA message board system was titled simply: "I hunt sys admins."
"Sys admins are a means to an end," it states. "Once you have control of the IT manager's computer then it's easy to monitor any "government official that happens to be using the network some admin takes care of."
Pwning the sysadmin is useful for malware attacks against large commercial routers and to defeat VPNs. The documents detail two pieces of NSA-developed malware, HAMMERCHANT and HAMMERSTEIN, which are designed to sit on routers and eavesdrop on VoIP traffic, and grab encryption keys to decrypt supposedly secure VPN connections, all in real time.
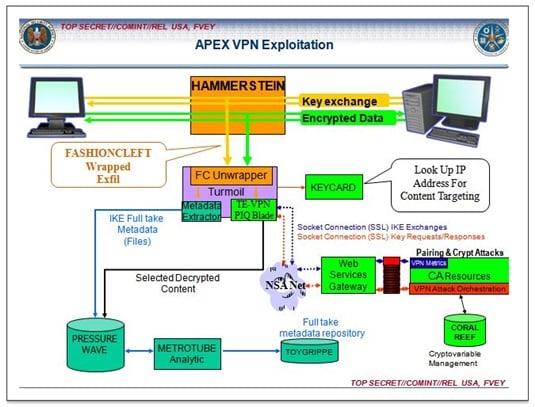
Taking the private out of VPN
Other malware includes code called QUANTUMSKY, developed in 2004, which can block access to websites, and a 2008 creation dubbed QUANTUMCOPPER which automatically corrupts any data downloaded by a user.
TURBINE is run though stations at the NSA's headquarters in Maryland, along with ancillary offices in the British Menwith Hill facility and from Misawa, Japan. Documents show the UK's GCHQ has been active in developing exploits for TURBINE and that it uses information gleans from the system, as do the other "Five Eyes" nations of Canada, Australia, and New Zealand.
"All of GCHQ's work is carried out in accordance with a strict legal and policy framework which ensures that our activities are authorized, necessary and proportionate, and that there is rigorous oversight," the British intelligence agency said in a statement.
